The Telnet protocol is capable of remotely managing network devices or computers over LAN or WAN. It is still popular today because it was one of the first protocols used with the launch of the Internet in 1969.
What is Telnet? What Does It Mean Exactly?
Telnet is an abbreviation of “teletype network,” “terminal network,” or “telecommunications network.”
TELecommunication NETwork, or Telnet, is one of the oldest tools on the Internet. It goes way back to the time of ARPANET. Telnet helps a computer connect to another computer far away on the network. It makes the computer you’re using act like a terminal connected to a distant computer.
All you need is a Telnet client. Think of a client as a unique program that makes your computer act like an old-style terminal but is now adapted to work with the Internet using the TCP/IP protocol.
Introduction to Telnet Protocol
Telnet is like a unique language that lets computers talk to each other on the Internet. It helps terminals connect and chat with a command interpreter on the server. Telnet uses a way to send information, kind of like messages, using a simple system that checks if everything is correct.
This way of doing things helps set up faraway computers. Imagine setting up a Cisco router with a special cable. After that, you can do the setup work from a computer far away, either on the same network or a different one. You don’t have to be right next to the device to make it work.
This is a simple way of doing things that other internet tools use, like FTP or email. It doesn’t talk about making sure you’re really you because that’s a different job for other programs.
But it’s not a super safe way to send information because the stuff it sends can be read by anyone on the way. When you use it to connect a faraway computer to one that acts as a server, it uses Port 23.
Apart from some extra choices and rules, this way of doing things is fundamental. It just sends bytes of information in a line, and when it sends the 255th byte, the next one is like a particular command. This Telnet way of doing things is described in detail in something called RFC 854.
How Does Telnet Work?
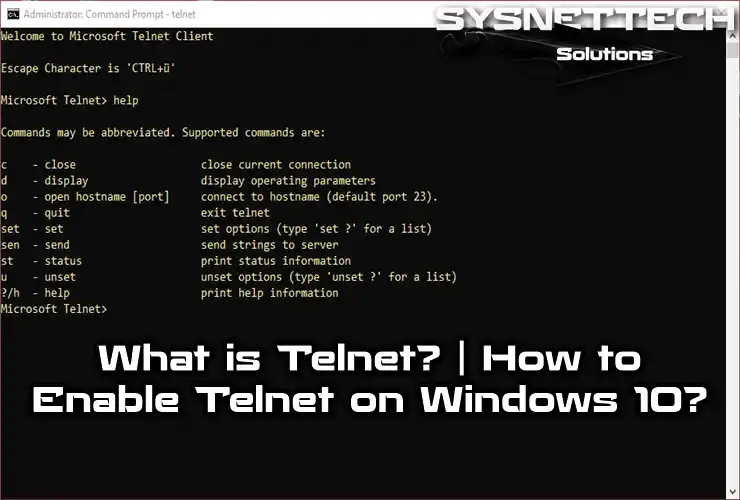
When you use Telnet, remember that its Client can work in two ways: Command mode and regular use mode. In Command mode, you can give specific commands that control how it works, like connecting and disconnecting.
These commands include:
- CLOSE: Closes the Telnet connection to the remote computer and returns to command mode (if started in command mode) or closes the application.
- QUIT: Sign out of the Telnet session. If you are connected to a remote computer, this command closes the connection and then the application.
- SET ECHO: If we cannot see what we are writing or, on the contrary, we double it, this command corrects the situation.
- OPEN: This command establishes a connection to a remote computer.
When our tool is in normal mode, it acts like a computer keyboard that talks to another computer. Each key we press gets sent to the faraway device, and what shows up on our screen is the reply from that other device.
If we want to switch from normal mode to command mode (for example, to end the session using QUIT), we have to press a particular button called the escape character. Then, we’re in command mode, and if we encourage CR or Enter, we go back to normal mode.
Telnet is only for text and doesn’t have pictures. But it’s helpful in fixing problems on a computer from far away without being there in person. People also use it to check information, like books, on machines connected to the Internet.
Apart from these uses, Telnet was commonly used to log in to UNIX machines (and it can still be used with the SSH version today). Many users with accounts on the machine could connect, log in, and work on that machine. This was a common way of working with UNIX systems.
Protocol Connection Details
With all that said, the first thing Telnet does on a faraway system is to connect or “login.” The program on your computer talks to the other computer and starts discussing how they’ll work together. To do this, you have to share some basic information with the program:
- Name: Refers to the server’s IP Address numerically or URL form—for example, 192.168.0.1.
- Port Number: Specifies the service you want to access on the server. An address with an additional port number allows access to not only the remote computer but also to a particular service or program within it. Unless otherwise stated, the default number is 23 (commonly used to connect to a user access account). During connection, the number can be added after the name or in a separate box, depending on the program.
- Terminal Type: Terminal identification is a contract used by both the client machine and the server with reference to the specific features and queues to be used. In this way, a virtual terminal is used regardless of what the physically abused terminal actually is. From the customer’s point of view, identification should be done in two parts.
- a: It is shown to the client program, which acts as a particular type of virtual terminal.
- b: It sets the type of terminal we will use on the server. This is a string of characters that is sent to the host during the connection negotiation.
- Login: In some services, login and password are not required because the server does not require them for that service.
- Password: The password that authenticates the user. You can enter your email address for general services that accept guests (visiting users).
- Log-Off: The last step at the end of a session on a remote system is to log out before the physical connection is interrupted so as not to leave a session open indefinitely on the host computer (it always consumes system resources). The concrete form depends on the system. There are no fixed rules, but on some systems, at the entrance, along with a welcome message, the appropriate word for disconnection is indicated. Usually, it is one of the following:
BYE, LOGOFF, LOGOUT, QUIT, END, EXIT, STOP. CLOSE first, the escape sequence comes. ABORT, escape sequence before (Use as a last resort).
Both Unix and Windows have their own Telnet client called Telnet.exe. If you’re using Windows, you can find it in the C:\Windows directory. This program comes with a helpful file called Telnet.chm, which has all the details you need to know.
Usually, people use Telnet to connect to big computers, like those at companies, universities, or research centers. These are often Unix machines. It’s not meant to connect to your neighbor’s computer over the Internet (other tools do that). People use Telnet for various reasons, from researchers continuing their work away from home to users requesting a service on a computer that can be accessed this way.
It’s important to note that you won’t connect to a regular PC but rather to giant machines with many users. For security, access is granted by the system administrator through something called an access account. This account comes with conditions, like when you can connect, which directories you can use, if you can write or just read, and how much information you can save. To identify users, a name (nickname) and a secret code (password) are used.
Knowing how to use Telnet on a remote computer is crucial after connecting. It’s not helpful to connect to a faraway machine if you don’t know the Operating System and the program you need to use at least a little bit.
Telnet Security Cases
Telnet isn’t the best choice for modern systems because of three essential security reasons:
- Telnet has many weaknesses that people have found over the years, and some still exist. This makes it not very safe for general use.
- Telnet doesn’t protect the information it sends, like passwords. So, if someone tries, they can easily see and save what’s being sent, using it for harmful reasons later.
- Telnet doesn’t have a secure way for two computers to talk and make sure no one else is listening in on the conversation. This lack of protection makes it risky.
SSH Issues
The main issue is security. When you use Telnet, all the usernames and passwords needed to get into computers travel on the Internet as plain text, which means they’re not hidden or protected. This makes it simple for someone watching the internet traffic to see and grab usernames and passwords to access these computers.
To fix this problem, SSH came into the picture a few years ago. It gained popularity because it’s like a safer version of Telnet. With SSH, all the communication between computers can be encrypted, meaning it’s like a secret code that keeps everything private during the session setup.
Where is Telnet Not Used?
Telnet is not a good choice when you need to keep things secure, especially on the Internet, because the information sent is not hidden or protected.
Imagine if you’re using Telnet between two computers. If someone can get close to the network devices, like routers or switches, they can quickly grab the information passing through. Tools like tcpdump and Wireshark make it quick for someone to see connection and password details.
Because of these problems, people stopped using Telnet and started using a safer option called SSH, which was introduced in 1995. SSH does everything Telnet does, but it adds strong encryption to keep your data secure.
Experts in computer security, like the SANS Institute and members of the Linux newsgroup, say you should avoid using Telnet for remote connections in regular situations.
When Telnet first appeared in 1969, Internet users were mainly in academic and research places, where security wasn’t a big worry. Only in the 90s, when internet use grew a lot, did people start caring more about security.
Using Telnet on networks with internet access can be risky because there are more people with internet access, and some might try to break into other people’s servers. So, it’s generally not recommended.
Nowadays
Today, people use Telnet to connect to BBSs (Bulletin Board Systems). These were initially accessed using a modem and a phone line. To connect to a BBS through Telnet, your computer needs to support things like ANSI graphics (a type of visual format) and file transfer methods. ANSI graphics are standard in BBS, and file transfer methods like ZModem help you send and receive files, like programs, games, or messages.
There are specific programs, called Telnet clients, that can do this. Some of them include mTelnet!, NetRunner, Putty, and Zoc.
You can set up and control all kinds of network devices using Telnet with the TCP/IP protocol. But, when you’re using Telnet, your data is not secure because it’s sent as clear text, which means it’s not protected. Instead of Telnet, many people prefer using the SSH protocol over the network for a safer experience.
How to Use Telnet?
To use Telnet, you first need to turn it on for the computer you want to control. Once it’s allowed, you can easily connect to that computer from somewhere else using the Command Prompt (CMD) through a specific port, TCP 23.
There are two parts to set up Telnet: the server and the Client. If you set up a server, you also need to install or activate the client service to connect to it from a distance.
Now, let’s see how to use Telnet in Windows 10. This article will guide you on connecting to an active Telnet Server on an ADSL Router after enabling the Telnet Client.
How to Enable Telnet on Windows 10
You can easily enable and use it on Microsoft Win XP, Vista, 7, 8, 8.1, and 10 operating systems.
Follow the steps below to activate/install the Telnet Client.
Step 1
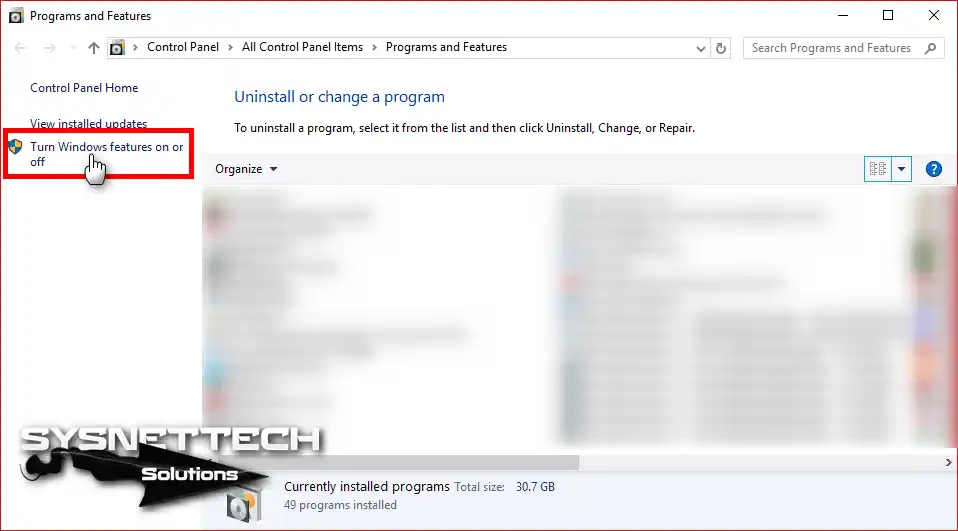
Right-click on the Start menu, and then click Programs and Features.

Step 2
In the Programs and Features, click Turn Windows features on or off.
Step 3
When the Windows features open or close window opens, select the Telnet Client option.
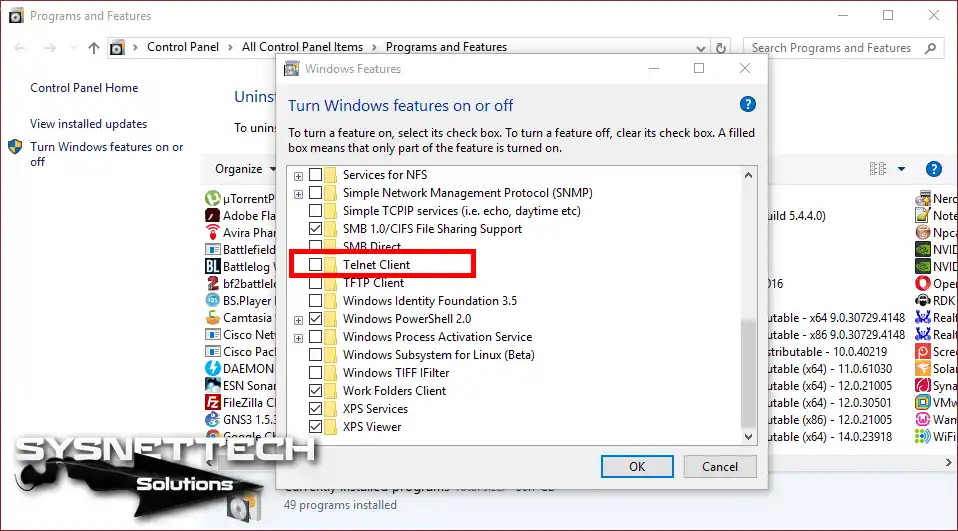
Step 4
After selecting the Client option, press the OK button.

Step 5
Applying changes to your system …
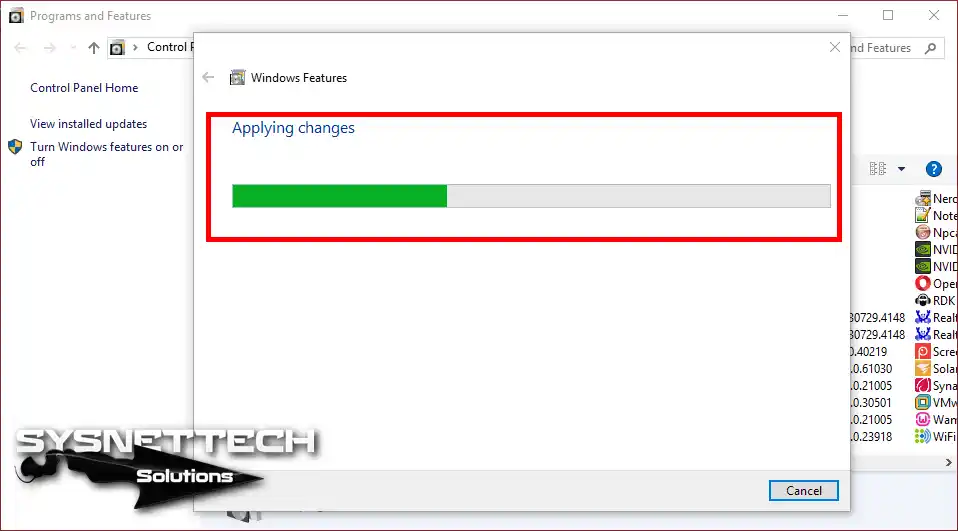
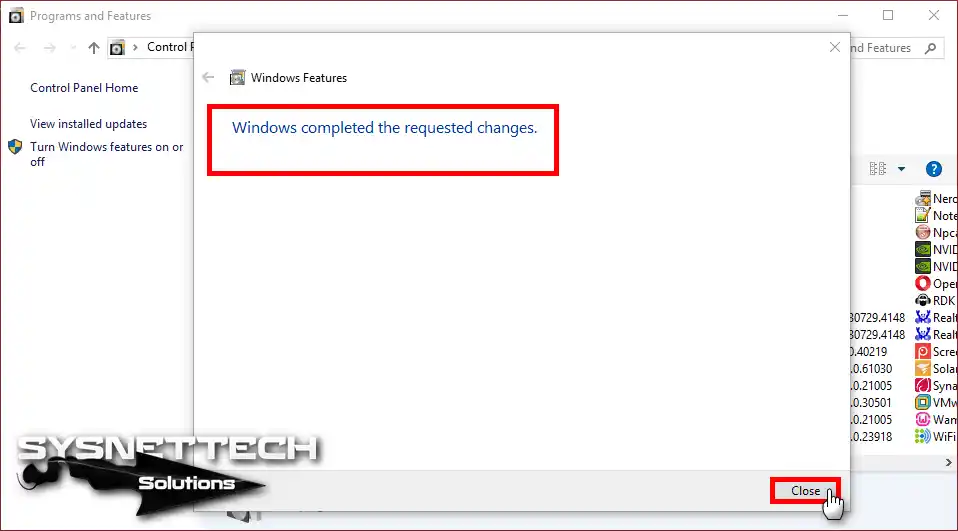
Step 6
After installing the service, click on the Close button.
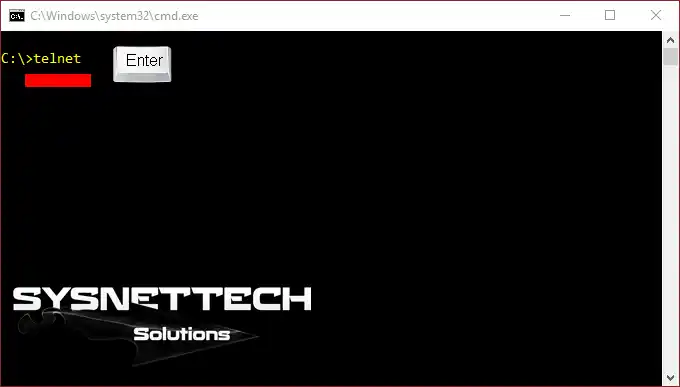
Step 7
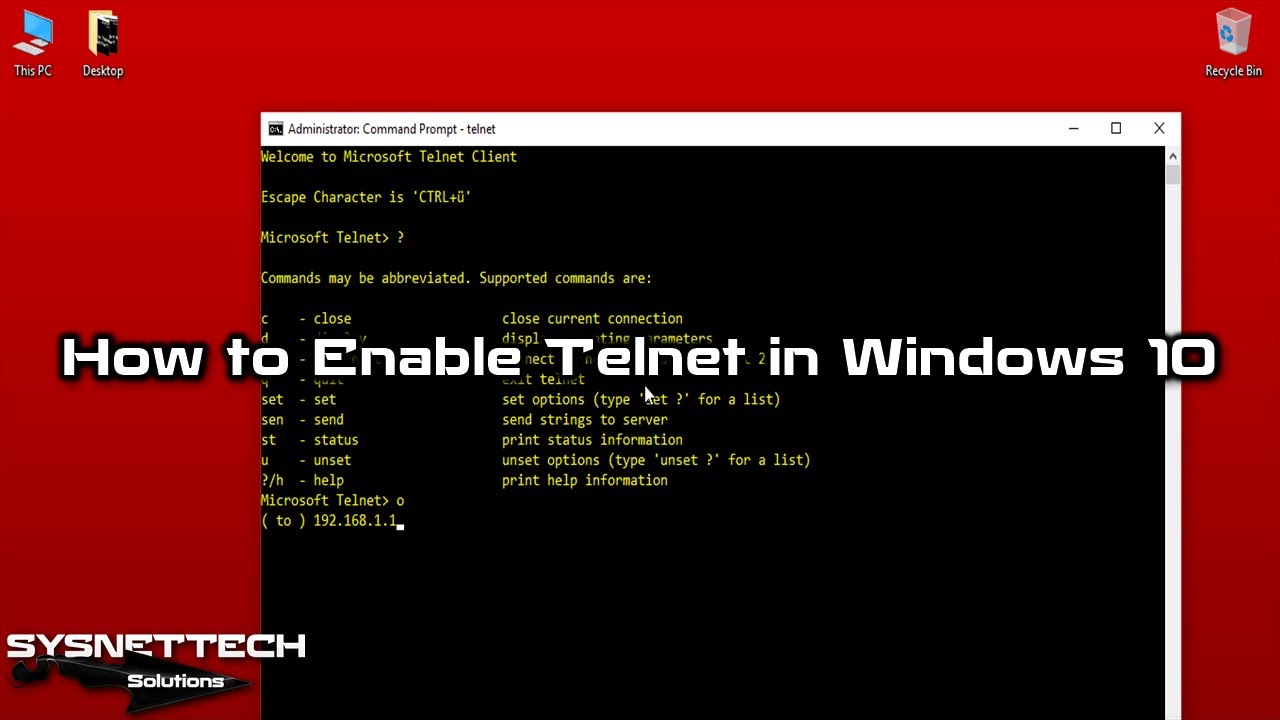
Open the Run by pressing the Windows Key + R together, type “cmd,” and press the Enter key. After running the CMD prompt, type “telnet” at the command prompt and press Enter to start this service.
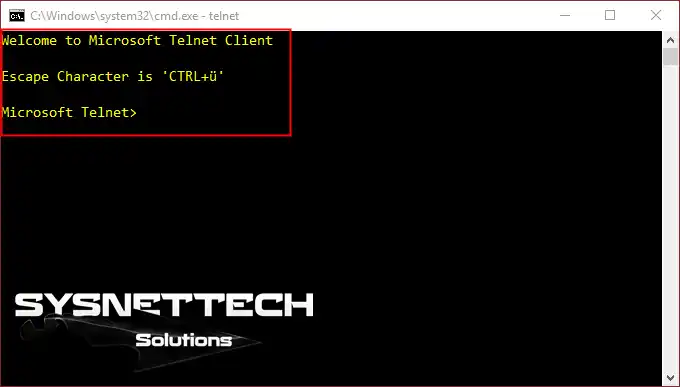
Step 8
After you see the welcome message, you can see that it works successfully.
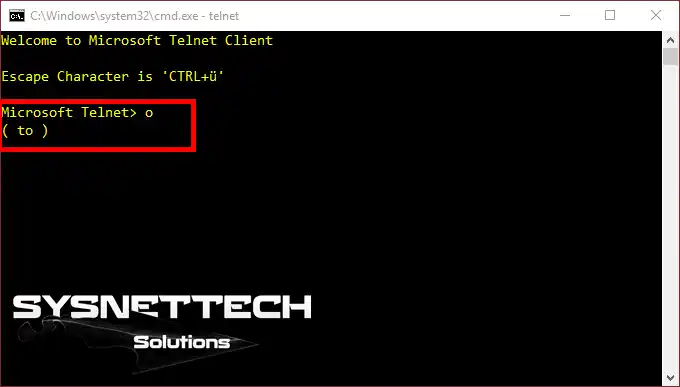
Step 9
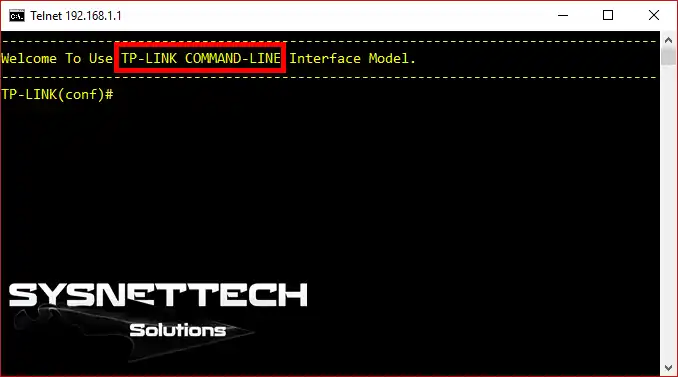
Now, type O (o) at the CMD prompt to connect to the ADSL Router on the local area network and press Enter.
Step 10
Type your default gateway IP address to access the ADSL Modem and press Enter.

Step 11
When you look at the image below, you can see a successful connection to an ADSL router using CMD.
How to Enable it using CMD
Another way to enable this service is to use the CMD command prompt. You can turn it on or off by using the CMD command prompt.
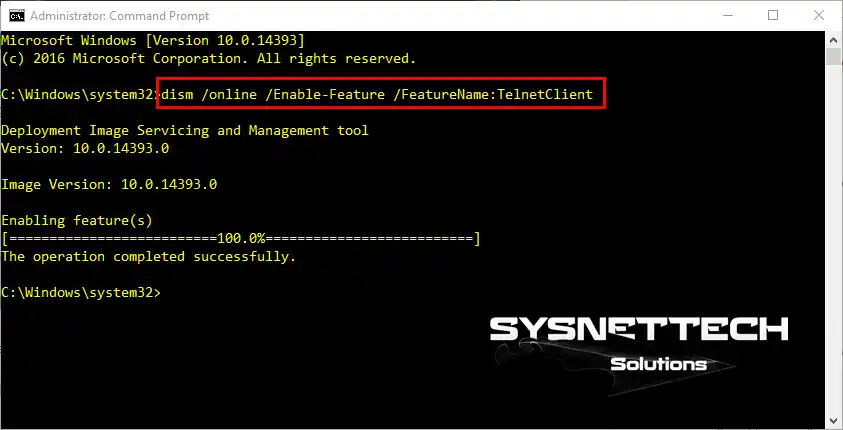
The DISM command is used on the CMD to activate the Client. Execute the command below to install Telnet with CMD on the Windows operating system.
dism /online /Enable-Feature /FeatureName:TelnetClient
How to Disable it using CMD
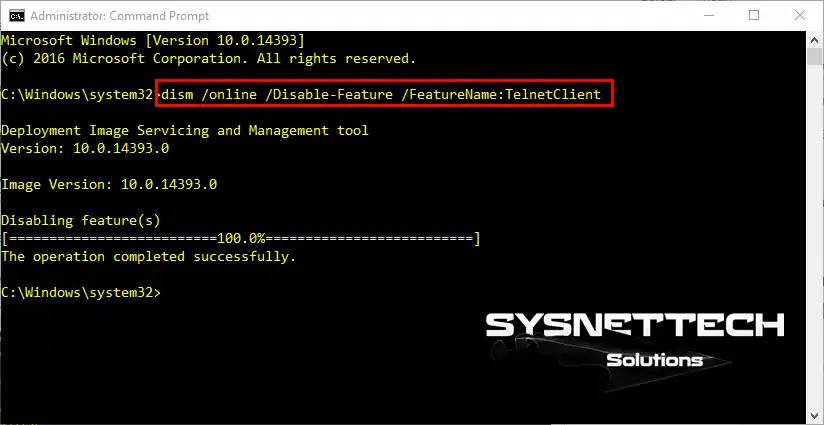
Use the following command to disable/remove Telnet.
dism /online /Disable-Feature /FeatureName:TelnetClient
Video
Final Word
In this article, we have defined the Telnet protocol used to manage remote devices in Windows operating systems and then enabled it. Thanks for following us!

Be the first to share your comment