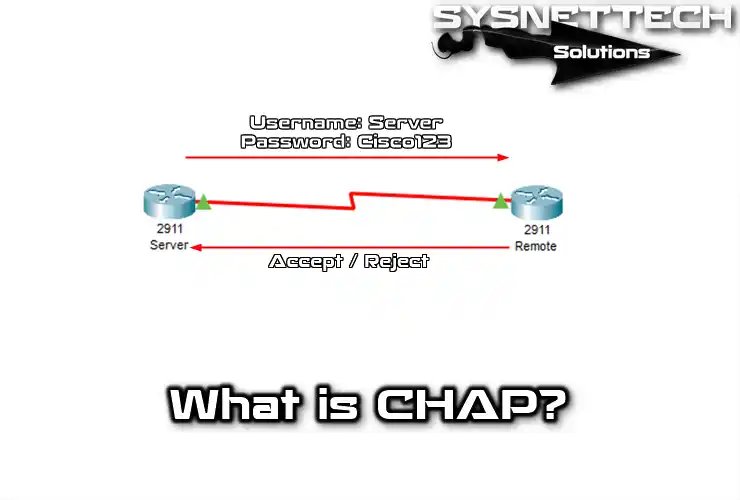
CHAP, or Challenge Handshake Authentication Protocol, checks who connects to a PPP server. The server asks the client who they are in three steps.
What is the CHAP Protocol that Provides Network Connection Security?
CHAP starts when two devices connect for the first time. Then, it uses a secret way to keep things safe when they talk to each other.
This protocol checks if a user or a server set up by the internet provider is genuine. They officially explained it in RFC 1994.
CHAP uses an ID and a value that changes. Because of this, it’s better at keeping away attacks than the PAP way.
Furthermore, it figures out a number that the remote device also knows, apart from how it checks who you are. It does this by using something called an MD-5 algorithm.
This way of confirming your identity always sends your username and password in a secret code. This method isn’t in the PAP way. That’s why the PAP method is less secure than CHAP.
The way it checks who you are asks the faraway server many times. This system sends a request for your identity to the device trying to join the network.
After that, the remote device uses a regular way of doing things that both sides know. It answers by sending a number after doing some math.
So, the server checks if this answer matches what it expected. If they fit, it sets up the connection. But if they don’t match, it ends the link.
CHAP Protocol History
The most basic history of the CHAP protocol goes back to the 1980s. Back then, networks were less complex. So, data was often not transmitted securely. Thus, the need for authentication protocols has increased to provide secure data transfer. So, developers first introduced it in RFC 1334 (Request for Comments).
In simple terms, CHAP’s primary goal is to make unencrypted methods of verifying who you are more secure. This adds a supplementary layer of protection when you use passwords.
They also made it for quick access to networks. The initial version strictly allows the client and server to check each other’s identity.
Later versions brought improvements in system security and performance. One of them is CHAP MD5. This improvement makes authentication stronger. In other words, MD5 encryption adds more layers of protection for data transfers.
Today, they still use the CHAP protocol in some institutions and companies. In particular, they consider it an example that gives strong protection in setups like getting in from far away and private online spaces (VPN).
CHAP Authentication Methods and Types
1. MD5 (Message Digest Algorithm 5)
It is the most common authentication method users use in the CHAP transaction. This stands for MD5 (Message Digest Algorithm 5) encryption algorithm.
In the MD5 method, an encrypted authentication process occurs between the server and the client. Thus, the client receives a random challenge value sent by the server. It then combines this value with its password and generates a hash with this algorithm.
It then sends the generated digest back to the server. Then, it performs the same operation, and if the calculated values match, the procedure is successful.
2. MS-CHAP (Microsoft Challenge Handshake Authentication Protocol)
MS-CHAP runs specifically on Microsoft-based systems. It is one of the most commonly used types of CHAP. This protocol offers more layers of security and key management.
3. MS-CHAPv2 (Microsoft Challenge Handshake Authentication Protocol version 2)
MS-CHAPv2 is a more current and secure version of the previous one. Thus, it contains a more robust encryption algorithm and supplies more security.
4. EAP (Extensible Authentication Protocol)
The EAP authentication type is a different version that works with CHAP. It can control things in many modes, making networks more flexible. Additionally, it allows you to experiment with various strategies as well.
5. PAP (Password Authentication Protocol)
The PAP method is less secure than CHAP. It sends unencrypted passwords, which weakens security. However, administrators might still use it in closed networks.
How Does the CHAP Protocol Work?
The CHAP method uses challenge-response for user authentication. Here’s how:
1. Initial Phase
After connecting, a procedure checks each person’s identity, ensuring mutual agreement. So, this occurs between the server and the client.
2. First Authentication Step
After setup, the server sends a challenge; the client scrambles it using a pre-determined method. This process ensures secure communication between them.
3. Client Response
The client generates an encrypted response using the received packet. It combines it with a password and challenge, then sends it back to the server for verification.
4. Checking the Response
In this case, the server examines its response to authenticate the client. Then, the algorithm responds with a known password. It checks if these two responses match, and if they do, it successfully allows the client to do so.
5. Successful Authentication
If the responses between the server and the client match, the authentication is successful. Thus, the client gains access to the network and begins to communicate securely.
Continuous Authentication
It repeats the authentication periodically during the connection period. This process increases data security. This makes it difficult for an attacker to capture the connection by intercepting the challenge packets.
CHAP Advantages and Disadvantages
Now, let’s look at the good and not-so-good sides of using CHAP for people who take care of networks and security:
Advantages
- Security
CHAP offers a powerful control method and uses algorithms like MD5 or MS-CHAPv2. This is very secure for authentication between the client and the server. Therefore, it does not send passwords in clear text. So it is more resistant to security threats.
- Advanced Options
It gives better security choices than others. MS-CHAPv2, in particular, provides more safety and locks things up even tighter.
- Flexibility
Being flexible means it can handle various ways to check things. One of them is CHAP EAP, which suits the different needs of network managers who want to ensure everyone is who they say they are.
Disadvantages
- Performance
This protocol needs more processing in the working process. It may be slower than other methods. But performance issues occur on large networks or high-traffic jobs.
- Password Update
It creates the need for users to update passwords regularly. In this case, it creates difficulties for users in password management.
- Transparent Text Encryption (PAP)
PAP is a type of CHAP, but it is insecure as it sends passwords in clear text. Thus, some users get the information over the network. As a result, you should use it on unsecured or closed networks.
A summary table:

Be the first to share your comment