Today, we use different ways to protect our important data on computers. We keep it safe by stopping people who shouldn’t see it from getting in.
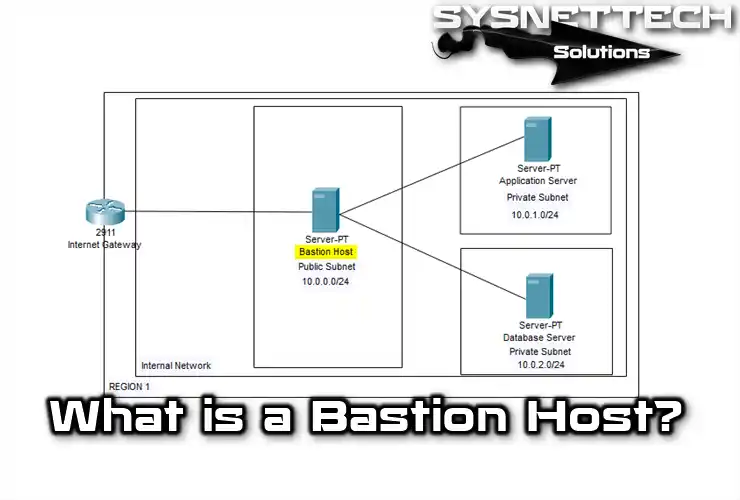
We need to focus on keeping corporate internal networks (Intranet) safe. In such an environment, we can use a central server to protect the internal network from the Internet. In this guide, I will explain what a bastion host is, how it acts as a guard, and its features and purpose.
What is Bastion Host? How Does a Host or Server Perform Its Function?
Bastion Host is a large part of the Intranet network’s firewall. Inside the firewall is the super powerful server. It is also the primary way that the internal area and the Internet talk to each other.
Imagine a super secure server, like the main gate. Thus, it protects the Intranet from Internet attacks.
The administrators set up this host to stop or control almost any network service. That way, they only allow specific Internet use. Therefore, no one should have an account on the machine. Because of that, they cannot use it to log in, control, or access the cyberworld.
Additionally, it is best to disable NFS (Network File System) on the remote system, which allows it to access files over the network. Also, make sure it can’t access the on-web portion of the Intranet. In other words, it prevents unwanted people from reaching the host.
This way, you stop intruders from messing up any piece of LAN. Set up defense servers to watch everything so internal admins know if there’s an attack.
System administrators typically keep two copies of the system log for security reasons. First, they hold a copy in case of tampering. Second, they always save it to use as a backup.
Another method to save a secure copy of the log is to connect it to the specific PC using the machine’s serial port. So, the PC’s only job is to monitor backup items.
How Does Bastion Server Protect Sensitive Networks?
Automated monitors are more complex than control programs. They usually look at the logs of the Bastion system. If they see anything strange, they raise the alarm.
For example, you can set it to send an alarm after three failed connections. Some hosts have control programs that actively investigate when they detect an attack against them.
You can do this by using the perfect program to check if anyone needs to keep everything the same on the machine. So, the control program calculates the number based on the size of the executable program on the server. Then, it periodically calculates the number to see if it has changed recently.
However, if the control number changes, it is a sign that someone is tampering with the software. As a result, it may show an attack from outside.
When the defense server receives a web page or email request from the client, it does not process it. Instead, it sends the request to the appropriately configured PC.
The main PC processes this proposal and then sends it back again. So, there can be many Bastion Host servers in the firewall. Each can even manage various Internet services for specific networks.
Sometimes, the host acts like a place people visit on the web. So, it offers Internet services safely using a proxy device or filtering router.
So, let’s say someone tries to break into the victim’s machine rather than another computer with different services. In this case, it will not affect other defensive hosts.
What is the Role of Proxy and Backup Servers Used with Bastion Host?

Backup servers are like companion servers in security installations. They are part of the proxy and firewall. Therefore, they stand between PCs on the Intranet and the web.
Proxy servers often work together with Bastion Host servers. Many Intranet PCs talk to the Internet through them. So this helps with security and makes it more secure than having many systems on the network.
Network administrators set up these backup servers for things like FTP, Web, and Telnet. However, they have to choose which cyberworld businesses will go through this system and which will not.
We have special software for each service on the backup machine. So, when the computer within the network requests something from the web, such as a web page, it talks to the Internet machine.
After that, the server sends the Web page content to the backup system. It then sends the data back to the requesting PC.
Proxy servers watch over everything between the Internet and the Intranet. A backup node can also watch every time someone connects to the Telnet service inside the private environment. That way, it decides how to handle the server on the web.
Also, the Proxy system keeps track of every IP address, the time it visits, the website it goes to, and how much data it gets. This helps us spot any network problems. It also allows LAN administrators to improve things for employees.
Purpose of Proxy Clients in the Network
However, some installations need specific proxy clients. These help with security plans as they can do more than just pass messages between the Intranet & Internet.
For example, you can set it up to send files from the Internet to the PC on the LAN. However, you can also send files from the company LAN to the web.
This way, administrators prevent people outside the company from obtaining business data. Or it prevents Intranet users from receiving files containing harmful viruses.
By saving data, system administrators make proxy servers run faster for some things on the Internet. For example, a web device holds many web pages. Whenever LAN users want, they can get speed from a proxy PC instead of the slower internet.
Frequently Asked Questions (FAQ)
- What is the purpose of the Bastion host?
- What is the difference between a firewall and a bastion server?
- What are the benefits of using the Bastion host server?
Conclusion
I want to say my last words about what a bastion is, that is, a central computer. The server in this physical structure acts as a bridge between the Internet and the Intranet network. Thus, it provides secure data flow both from inside to outside and vice versa.
On the other hand, it works well with backup and proxy servers. When these come together, we can easily monitor IP traffic on the network. In this case, we ensure the security & integrity of our LAN.

Be the first to share your comment