Ping (Packet InterNet Groper) is a tool used to verify that a network data packet was successfully delivered to its destination. You can also use it to check the network connectivity of a computer on a network or any device connected to the network.
What is Ping, and What Does It Do?
Ping is an abbreviation of “Packet InterNet Groper.” In short, we use it to test network problems. You can ping a device connected to the network to test its connection. For example, you can check the network connection by pinging a computer on the LAN network or the WAN side.
Mike Muss developed the Ping protocol in 1983. This protocol sends 32-byte packets to the target and checks the connection. If you ping a nearby server, the response time will be low. However, if you ping a distant server, the response time will be higher.
The Ping protocol uses the Internet Control Message Protocol (ICMP). It transmits an Echo Request packet to the target and waits for an Echo Reply packet. If the client receives an Echo Reply, the connection is successful. As a result, the ping operation verifies the network connection.
What is ICMP?
ICMP (Internet Control Message Protocol) is a sub-protocol for error reporting and IP control. Therefore, it sends error messages indicating that a service is not available or a router cannot be found.
ICMP is different from the TCP layer and the UDP structure because it is not usually used directly by network users. However, Ping and Traceroute tools test the availability of a host using ICMP. They also determine the time it takes for packets to reach that host and the number of hosts it passes through. As a result, ICMP plays a critical role in identifying network errors.
How Does It Work?
ICMP is part of the IP protocol suite and is defined in RFC 792. ICMP messages work in response to errors in IP datagrams. We also use it for diagnostic and routing purposes.
The ICMP version for IPv4 is ICMPv4. However, there is an equivalent protocol for IPv6, ICMPv6. ICMP messages operate at the network layer level. So, IP encapsulates the appropriate message with a new IP header and transmits the datagram.
For example, every Router that transmits an IP datagram decrements the TTL field by one. If the TTL reaches 0, it sends an ICMP “Time to Live Exceeded” message. However, ICMP messages are encapsulated in a single IP datagram and are not guaranteed to be delivered.
ICMP messages are included in IP datagrams and act as a particular case of normal IP operations. ICMP checks whether a packet can reach its destination when it reaches its lifetime. It also detects network errors and prevents or corrects related problems.
Most network utilities rely on ICMP. The traceroute command uses UDP datagrams with particular TTL IP fields. The ping tool uses “Echo request” and “Echo reply” messages. In conclusion, ICMP does a serious job of keeping networks running smoothly.
Protocol Format
List of allowed control messages:
| Code | Message Type |
|---|---|
| 0 | Echo Reply |
| 1 | Reserved |
| 2 | Reserved |
| 3 | Destination Unreachable |
| 4 | Source Quench |
| 5 | Redirect Message |
| 6 | Alternate Host Address |
| 7 | Reserved |
| 8 | Echo Request |
| 9 | Router Announcement |
| 10 | Router Request |
| 11 | Time Out |
| 12 | Parameter Problem |
| 13 | Timestamp |
| 14 | Timestamp Response |
| 15 | Request for Information |
| 16 | Information Response |
| 17 | Request for Address Mask |
| 18 | Address Mask Response |
| 19 | Reserved for security |
| 20-29 | Reserved for robustness experiments |
| 30 | Traceroute |
| 31 | Datagram Conversion Error |
| 32 | Mobile Host Redirection |
| 33 | IPv6 |
| 34 | IPv6 |
| 35 | Mobile Registration Request |
| 36 | Mobile Registration Response |
| 37 | Domain Name Request |
| 38 | Domain Name Response |
| 39 | SKIP Discovery Algorithm Protocol |
| 40 | Photuris, Security Bugs |
| 41-255 | Reserved |
For a complete list of ICMP parameters, see the list published by IANA.
How to Use Ping?
You can use Ping using the Command Prompt on Windows XP, 7, 8, 8.1, 10, and Windows 11. Follow the steps below to use this simple network tool.
Steps:
Step 1
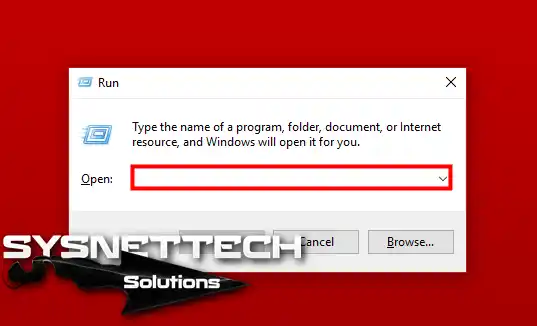
First, open the Run tool by holding down the Windows-looking key on your main computer and pressing the R key.
Step 2
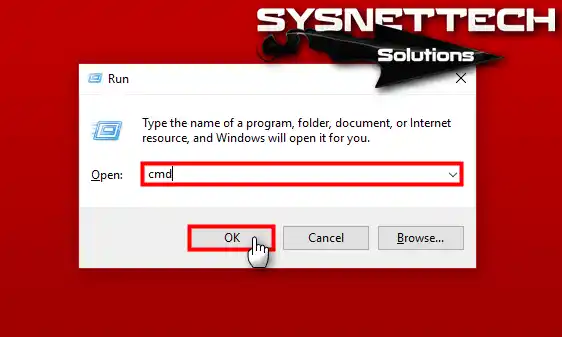
In the Run window, you will see the section that says Open. Here, type “cmd” in the text box and then click OK.
Step 3
When you start the CMD (Command Prompt) tool, you will see a screen like the one below on your system.

Step 4
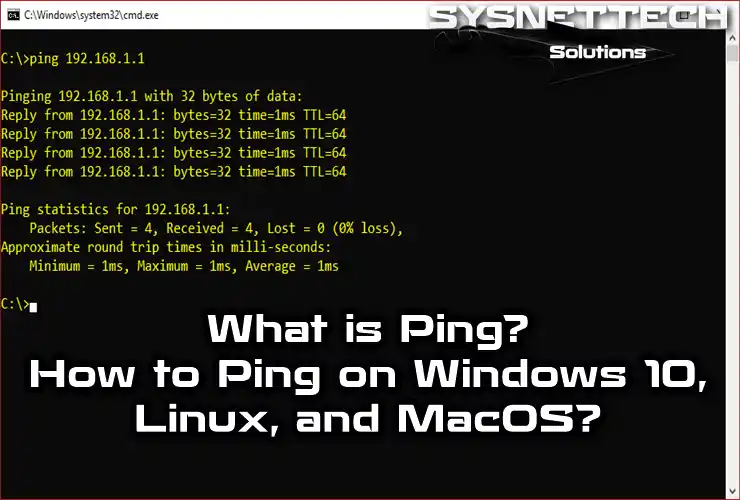
To ping your ADSL modem’s IP address, type ping 192.168.1.1 in the CMD and press Enter. However, your default gateway IP address here may be different.
If the test is successful, as in the image below, it means you have a connection to your ADSL modem on your network.
The output ( 0% loss ) indicates that the packets are being transmitted without any problems. The part that says Bytes=32 indicates that Ping sends 32-byte packets by default.

Step 5
What is Destination Host Unreachable?
When you ping a client that is down on the network, you will receive a Destination Host Unreachable message. The main reasons for the Unreachable message are:
- When the target machine is down, you get the error Target Machine Unreachable.
- When there is an error in the target machine’s TCP/IP configuration, you get this error.
- When it finds the target network but cannot find the target client, you get this error.

Step 6
What is Request Timed Out?
If you ping a client that is not on the same network, you will get a Request Time Out error.
For example, let’s say you are successfully pinging all clients on the 192.168.1.0/24 network. But you are unable to ping a client on the 192.168.2.0/24 network, and you get this error. At this point, you are definitely not able to reach your target.
The main reasons for the Request Time Out error are:
- When the target is down, you will get the Request Timed Out error.
- If the target client is known but you still cannot ping it, you will also get this error due to a Routing protocol error on the wireless Router.
- If there is a firewall installed on the target, you will also get this message because it blocks ICMP packets.

Step 7
How to Ping a Website?
It is straightforward to ping a website. The purpose of testing the website’s connection is to check whether it is online or not. Similarly, open the CMD prompt, and after selecting a website that you want to ping, type the following command and press Enter.
When you examine the image below, you can see that the website can be accessed successfully.

How to Ping on Linux?
Pinging is also relatively easy on Linux-based operating systems such as Ubuntu, Fedora, Linux Mint, Debian, and Kali Linux. The process you use on Windows systems is the same.
To ping on Linux/Ubuntu, open Terminal by pressing Ctrl + Alt + T keys together. Apply the following command in Terminal.
As you can see in the image below, the connection test will be continuous on Ubuntu.

Also, to ping a website on Linux, type the name of that website.

Another example is specifying the number of packets. You can specify the number of packets to be sent to the destination by adding [ -c number ] to the command.

How to Ping on macOS?
There are two different methods to ping on all macOS systems running on a MacBook or an iMac. The first method is to use Terminal on macOS. The second method is to use the Network Utility tool of macOS.
To ping via Terminal on macOS, first open Terminal. Press the Windows Key + Spacebar together to open the Terminal. Type terminal in the search box, find the program, and run it.

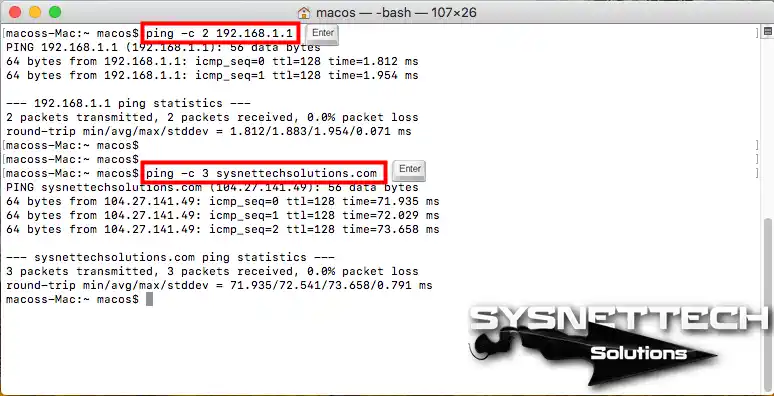
Once you open Terminal, you can ping the IP address continuously using the ping 192.168.1.1 command.

You can add the [ -c + number ] command to ping an IP address or website as many times as you specify.
You can also test the connection to an IP address or website using the Network Utility program on macOS. Type network utility in the search box and find and open the program.

Click on the Ping tab, and after filling in the required fields as in the image below, you can use the Ping command with the Network Utility.

Ping Usage Video Tutorial
Windows Video 1
Linux Video 2
macOS Video 3
Frequently Asked Questions (FAQ)
- What does ping mean, and how does it work?
- Why do we ping?
- What does a ping test show?
- Why is ping important?
- What can affect ping results?
Conclusion
In conclusion, Ping and ICMP are vital in maintaining network connectivity. We also often use them to diagnose network problems. For example, network administrators can verify that devices are reachable with Ping. However, they can also troubleshoot connectivity issues at the relevant location.
In short, understanding ICMP messages and codes is essential for interpreting network errors. In addition, you should know and use them to ensure smooth network operations. Knowing how to use Ping and how to analyze the results gives network professionals an advantage. As a result, you can effectively manage and optimize your network infrastructure.


Be the first to share your comment