In today’s computer networks, network redundancy is significant. The continuity performance of network devices that are well configured on the network increases at the maximum level. Connecting the switches with more than one network cable means network redundancy.
What is STP?
In a well-designed network, an error has become almost impossible. The reason for this is the design and development of backup networks. Therefore, if an institution that provides a good service or market reputation experiences an inability to provide services to its customers, it will lead to loss of customers and reliability as well as commercial loss.
Layer 2 Switches used for data transmission on the network create a Loop on the network when backup ties are not correctly configured. For example, You have connected two Switches with two network cables, but you have not configured them with STP. This is to create a random backup network.
In fact, the purpose here is to automatically switch on the other cable in case of a fault in a cable. If we give more detailed information, it is the shortest way to transmit the frames over the fastest link.
In the previous article, we provided detailed information about network redundancy and mentioned the problems that arise in the network backup process. The biggest problem with these problems is Loop. We can also say Broadcast Storm.
The following image is a small network topology that forms a Loop;
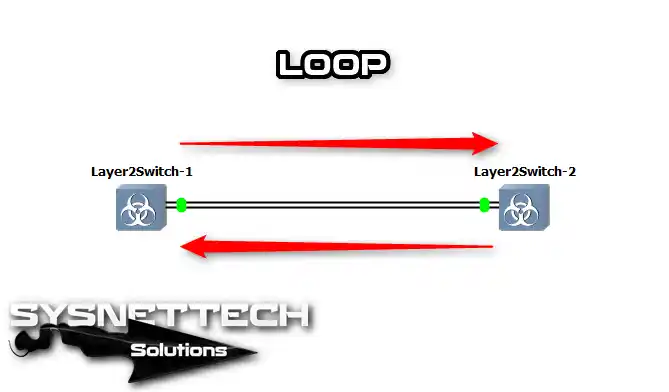
If we explain the picture above, let’s assume that they are computers connected to the Switch. Because these computers do not have MAC addresses, they broadcast (ff:ff:ff:ff:ff:ff) over the network via the ARP protocol. Switch2, receiving the broadcast frame, transmits all frames except for the interface it receives.
As a result, Switch2 will transmit the Broadcast frame back to Switch1, and ARP traffic will be generated because the computer that receives the Broadcast frame will send the Broadcast frame in the same way. Therefore, a loop will occur on the network, and the Loop will continue as long as one of the two switches is not turned off. You can prevent the loop by removing one of the two cables connected to the switches.
Well, why is this Broadcast framework going to last forever? Because Ethernet Frames do not have a TTL (Time to Live) value.
At this point, STP (Spanning Tree Protocol) will come into play.
Working Logic
STP (Spanning Tree Protocol) chooses the best path as well as preventing loops on the network. Although the operational logic of the STP is mainly mixed, it is straightforward to configure on Switches.
The STP uses the Spanning Tree Algorithm (STA) algorithm to avoid Loops.
Let’s briefly describe how the STP Protocol works;
- It backs up (standby) or blocks specific interfaces configured on the switch as backup connections.
- It puts the interfaces for the latest devices in the Forwarding mode.
- It transmits the packet by determining the most suitable route in case of failure of the forwarding path.
After the STP is enabled on the switches, the STA algorithm configures a map of the Switches. The STA algorithm uses some terms to determine the backup path or the best path for transmission of the data packet.
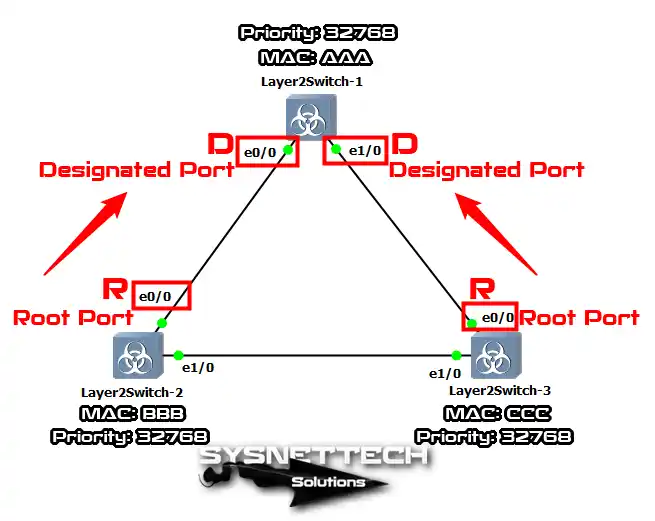
When we look at the image below, we see that 3 Switches are connected. In a Spanning Tree Protocol-configured network, Switches send packets called BPDUs between themselves. The switch that is selected as the Root Bridge sends BPDU (Bridge Protocol Data Units) packets to every other switch on the network every 2 seconds.
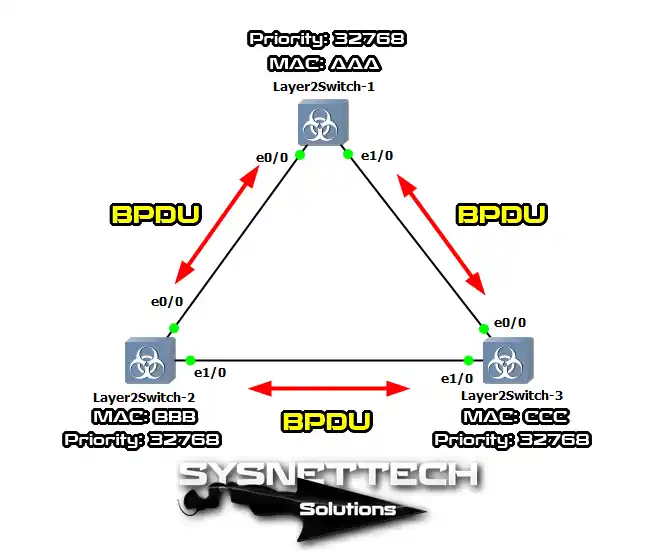
A BPDU framework contains the following information;
- Source Switch Identity Information
- Source Switch Port Information
- Root Bridge Outbound Path Total Cost
- Maximum Data Packet Timer Value
- Hello Package Information
As explained in the above image, BPDU frames will be sent between Switches every 2 seconds. If you like, you can change the default hello packages. How was the Bridge ID value set for the selected Switch as the Root Bridge?
How Does Select Root Bridge?
In fact, all switches are root bridges, and the default priority value of all switches is 32768.
When setting the Bridge ID value, the MAC Address and Priority value are considered. If all switches have the same default priority value, the Bridge ID is determined by looking at the MAC addresses. In the above view, the smallest MAC address is AAA, and the Switch-1 with the smallest MAC address will have the best Bridge ID value and, therefore, will be the Root Bridge.
The interfaces defined as Root Bridge always function as Designated, which always means Forwarding.
In the following image, Switch-1 is the Root Bridge, and Designated ports are also indicated by the letter “D.”
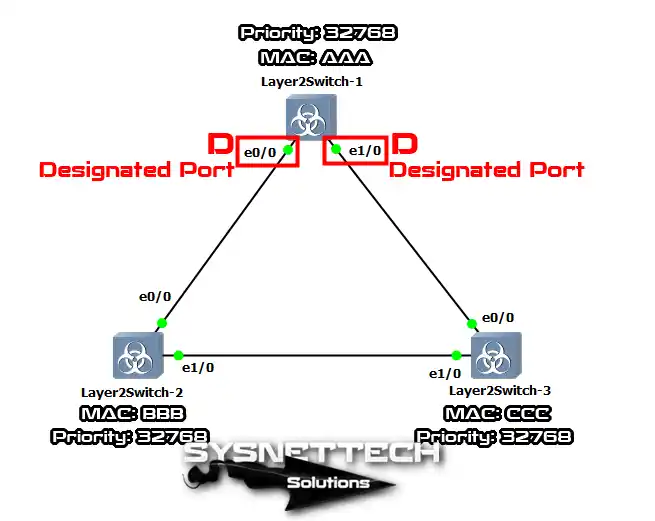
How Does Select Designated and Root Ports?
In the Spanning Tree Protocol configuration, the shortest path to the Root Bridge Switch is called the Root Port. Therefore, the Switch-2 and Switch-3 Ethernet0 / 0 interfaces above will be configured as Root Ports.
Spanning Tree Root Port is used to select Path Cost. Under normal conditions, the Path Costs assumed by the IEEE are calculated as follows when calculating with the Bandwidth / 1000 formula.
| Bandwidth | Path Cost |
| 4 Mbps | 250 |
| 10 Mbps | 100 |
| 16 Mbps | 62 |
| 45 Mbps | 39 |
| 100 Mbps | 19 |
| 155 Mbps | 14 |
| 622 Mbps | 6 |
| 1 Gbps | 4 |
| 10 Gbps | 2 |
In addition, each Switch connection must have one Root Port. In the following example, the closest interfaces to the Root Bridge are designated as Root Ports.
After reviewing the Root Ports, we will look at Switch-2 and Switch-3 Ethernet1/0 interfaces.
How Does Select Designated and Non-Designated Ports?
When the Designated Port is selected, the MAC Address and Priority values are examined. If the priority values of both switches are equal, the MAC addresses for the Designated Port will be checked.
In the following example, when Switch-2 is selected as the Designated Port, the other Switch will be chosen as Non-Designated/Blocked to prevent looping.
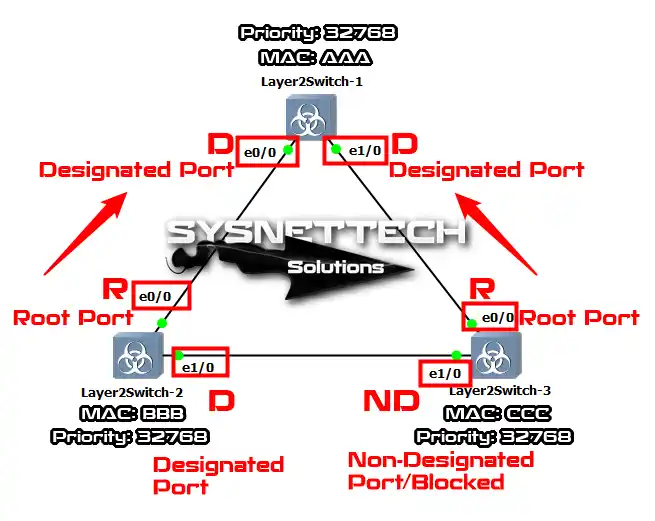
Once Designated and Non-Designated/Blocked Ports are identified, Loop will no longer occur in our network. In the above images, the connections between Switches have the same Path Cost values. Therefore, these ports may vary in a network that spans more than one Switch. Also, the selected Port-Orange will be Non-Designated/Blocked.
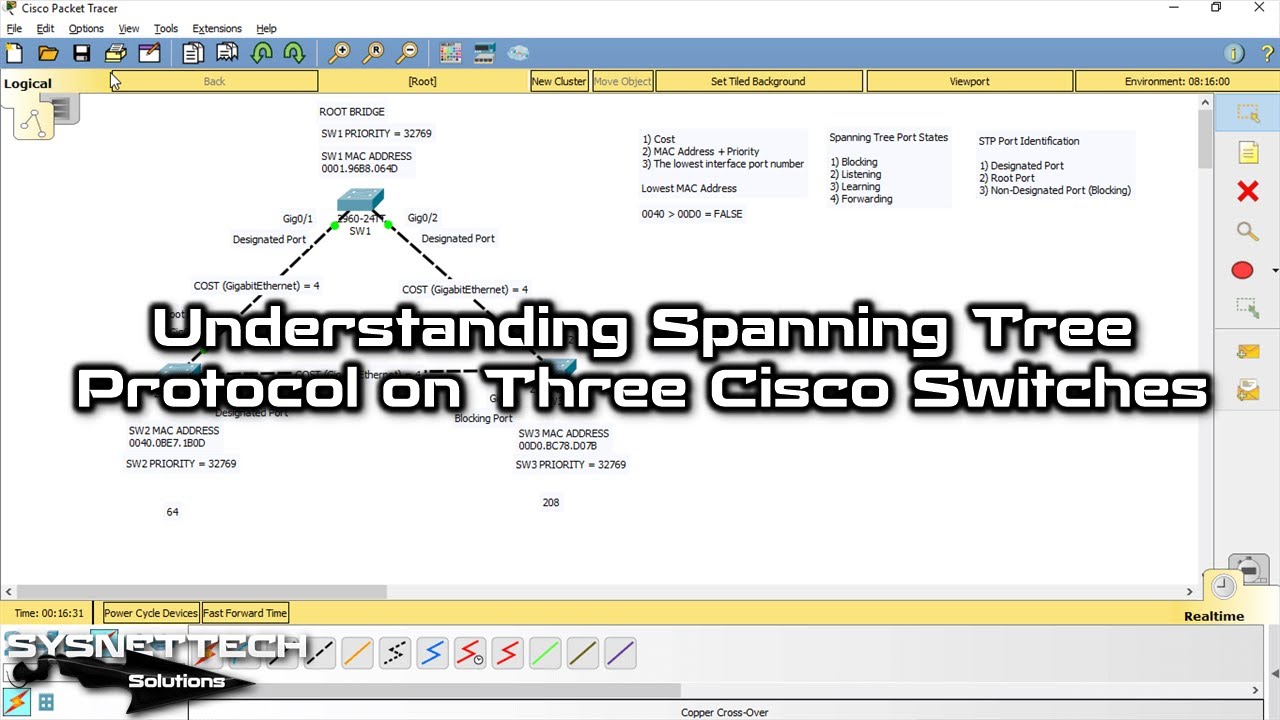
Understanding Spanning Tree Protocol in Packet Tracer
To better understand the Spanning-Tree protocol, we will examine the STP details by adding 4 Switches in the Cisco Packet Tracer program.

When we examine the network topology above, we can see that all Switches have the same priority values. Therefore, the STP will select the Switch with the lowest Bridge ID value as the Root Bridge by evaluating the MAC address when selecting the Root Bridge.
- Once the Root Bridge is selected, the interfaces bound to its ports will be Designated Ports because the links to both bridge switches are in the root state. The next step is to select Root Ports.
- If Root Ports is selected, the Path Cost to the Root Bridge Switch is considered. If Path Costs are equal, Switch0 and Switch3 will be designated as Root Ports. For example, If the path cost value between Switch3 and Switch2 were 19, the connection to the Root Bridge from Switch3 would enter the Non-Designated/Blocked state.
- Once the Root Ports have been defined, the Switch1 bindings will be configured. If so, the outgoing Path Cost is calculated from the Swictch1 Root Bridge. If Path Cost equals (4 + 4), Switch1 MAC Address and Priority are examined. According to the topology above, the Priority values are equal, and therefore, the MAC Addresses are considered. Switch1, Switch0, and Switch3 look at Bridge ID values and set the lowest value Switch0 as the Root Port.
After that, a single interface will remain, and this interface will be configured as Non-Designated / Blocked to prevent loops. As a result, the STP designs the network map by sending and receiving BPDU frames on the network to and from other switches.
STP YouTube Training Video
After connecting three Cisco Switches with a cross cable in Cisco Packet Tracer, you can watch the video below to examine the STP convergence and also subscribe to our YouTube channel!
Conclusion
On the Network Switches, the STP is enabled by default and automatically selects the path. However, it is essential to manually configure the management of the switches on the network. Management of Cisco Switch BPDU packages is critical in terms of security.

Be the first to share your comment