After you create VLANs on a Switch using Cisco Packet Tracer, you must communicate data between the VLANs.
You must configure Inter-VLAN Routing to communicate with clients that are members of different VLANs on the Layer 2 Switch.
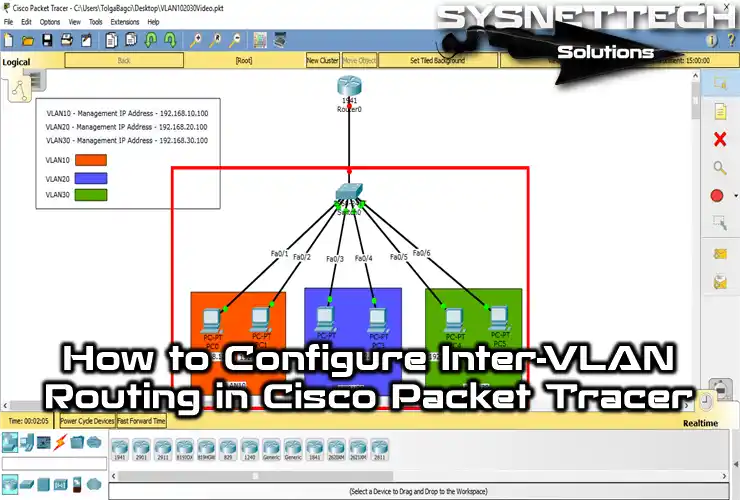
How to Configure Inter-VLAN with Router-on-a-Stick on Packet Tracer
What is Router-on-a-Stick?
Router-on-a-Stick is the second type of Inter-VLAN routing, and the Router is connected to the Switch with a single interface. The Switchport connected to the Router is configured as a trunk port.
In order to enable routing between VLANs, subinterfaces are created according to the IP addresses of the VLANs in the interface connected to the Switchport of the Router, and routing is provided. The subinterface configured interface accepts traffic from all VLANs.
If there is a Layer 3 Switch in the network environment, all you need to do for routing to VLANs is to execute ip routing in config mode.
Another way to enable VLAN routing is to plug more cables from the Switch into the Router. This method is not recommended as using more cables will result in both reducing the number of empty interfaces on the Router and increasing the cost of the cable.
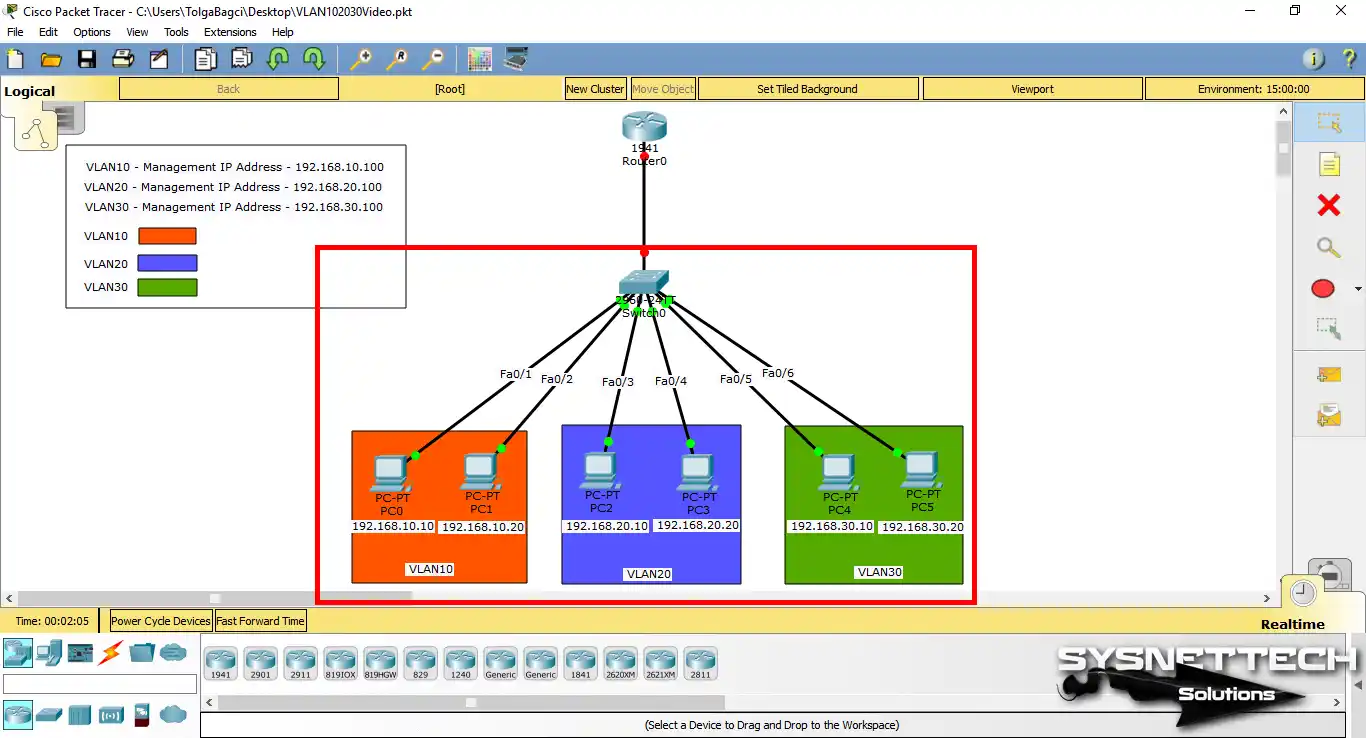
Now, create a network topology as in Step 1 on the Cisco simulator software. After designing your network topology, create VLANs called VLAN10, VLAN20, and VLAN30 on the Cisco Switch and add management IP addresses.
Follow the steps below to enable routing between the new VLANs you have created.
VLAN Routing on Cisco Switch
Step 1
After creating a network topology like the one in the following image, click Router for Inter-VLAN Routing and open the CLI.
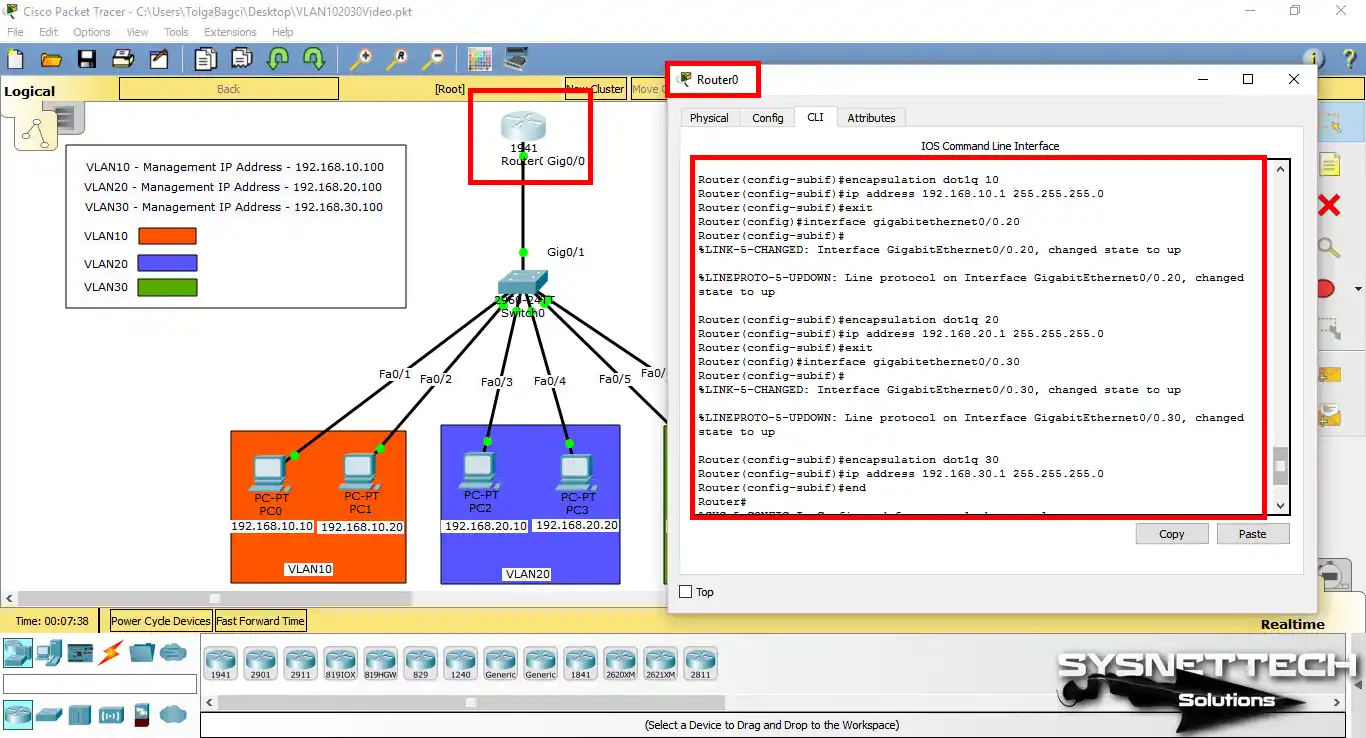
Step 2
At the CLI command prompt of the Cisco Router, execute the following commands to create a Subinterface for the interface that connects to the Switch.
When creating a subinterface, you can type the number of the VLAN ID to avoid confusion next to the port and slot number of the respective interface. For example, gigabitethernet0/0.10 is a subinterface targeted at VLAN10.
Router#conf t
Router(config)# interface gigabitethernet0/0
Router(config-if)# no ip address
Router(config-if)# no shutdown
%LINK-5-CHANGED: Interface GigabitEthernet0/0, changed state to up
%LINEPROTO-5-UPDOWN: Line protocol on Interface GigabitEthernet0/0, changed state to up
Router(config-if)# exit
Router(config)# interface gigabitethernet0/0.10
%LINK-5-CHANGED: Interface GigabitEthernet0/0.10, changed state to up
%LINEPROTO-5-UPDOWN: Line protocol on Interface GigabitEthernet0/0.10, changed state to up
Router(config-subif)# encapsulation dot1q 10
Router(config-subif)# ip address 192.168.10.1 255.255.255.0
Router(config-subif)# exit
Router(config)# interface gigabitethernet0/0.20
%LINK-5-CHANGED: Interface GigabitEthernet0/0.20, changed state to up
%LINEPROTO-5-UPDOWN: Line protocol on Interface GigabitEthernet0/0.20, changed state to up
Router(config-subif)# encapsulation dot1q 20
Router(config-subif)# ip address 192.168.20.1 255.255.255.0
Router(config-subif)# exit
Router(config)# interface gigabitethernet0/0.30
%LINK-5-CHANGED: Interface GigabitEthernet0/0.30, changed state to up
%LINEPROTO-5-UPDOWN: Line protocol on Interface GigabitEthernet0/0.30, changed state to up
Router(config-subif)# encapsulation dot1q 30
Router(config-subif)# ip address 192.168.30.1 255.255.255.0
Router(config-subif)# end
Router#
%SYS-5-CONFIG_I: Configured from console by console
Router# wr
Building configuration...
[OK]
Router#
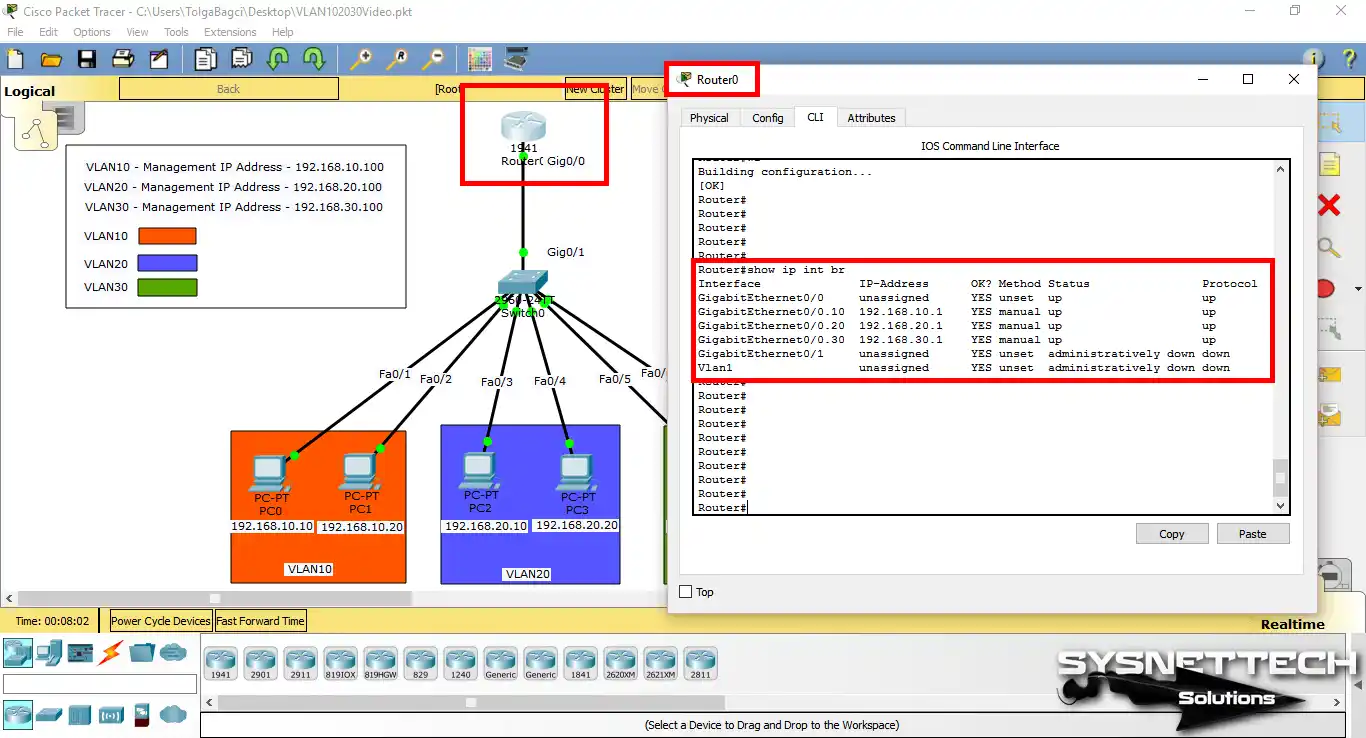
Step 3
After creating the subinterface on the Cisco router, check its status by executing the show ip interface brief command at the CLI prompt.
Step 4
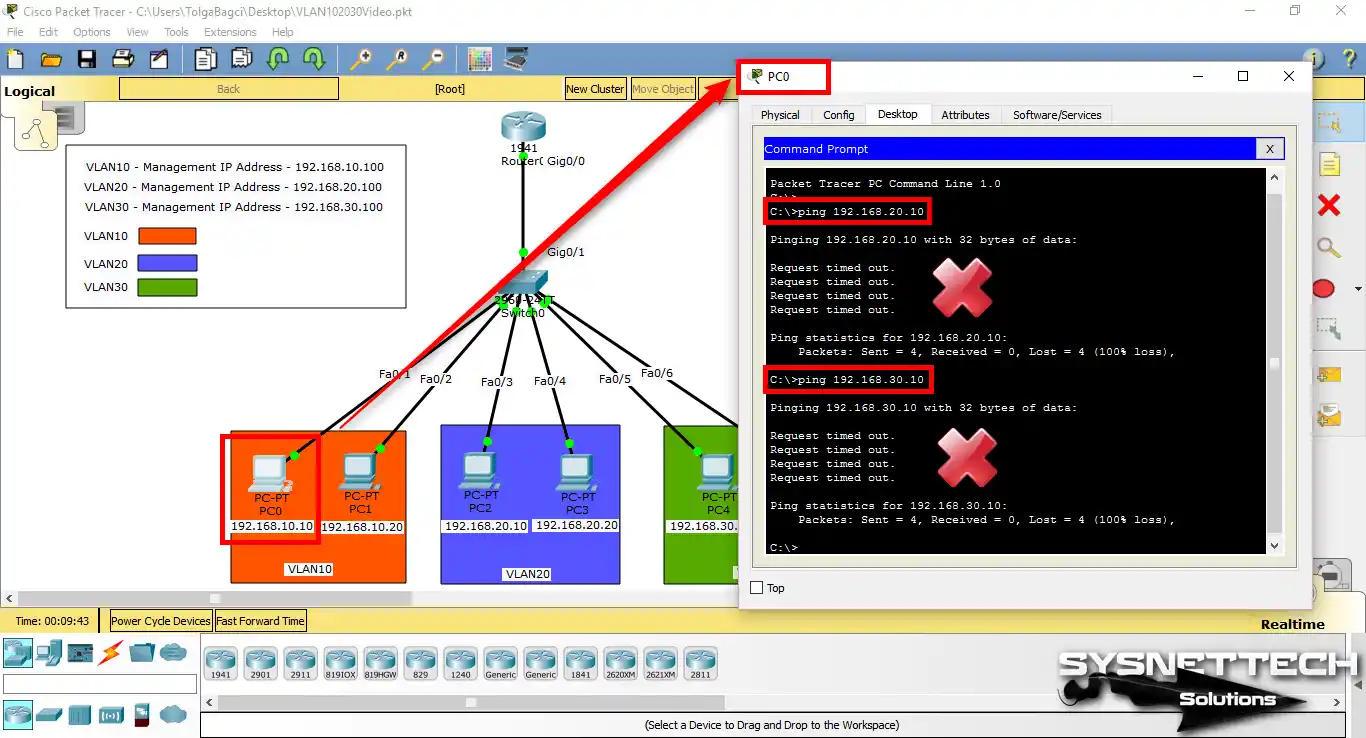
Click PC0 in the workspace and open Command Prompt from the pop-up window. When you ping VLAN20 and VLAN30 member PCs from PC0, you will see that the operation failed.
The reason the ping failed is that the Cisco Switch Gig0/1 interface that is connected to the Cisco Router is not configured as TRUNK.
Step 5
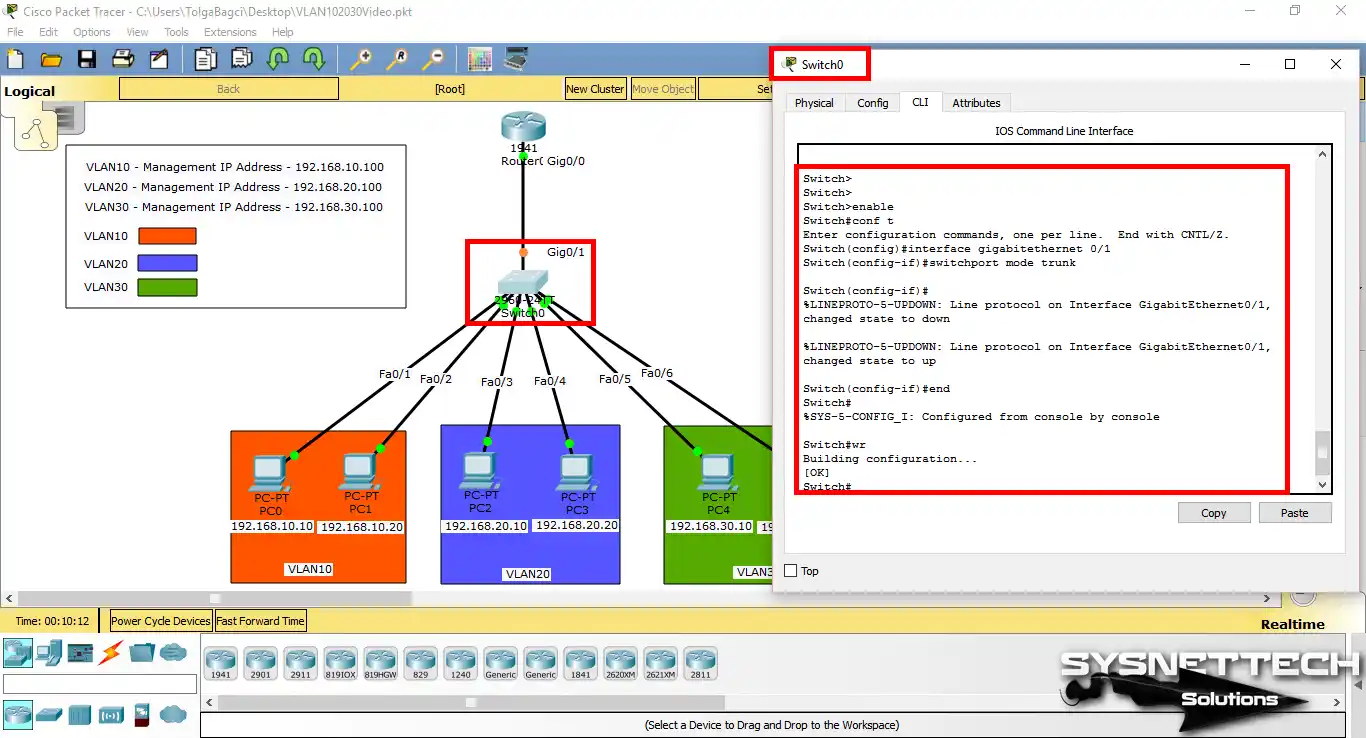
To configure the GigabitEthernet0/1 interface as a TRUNK port on the Cisco Switch, execute the switchport mode trunk command in the config mode of that interface.
Switch# conf t
Enter configuration commands, one per line. End with CNTL/Z.
Switch(config)# interface gigabitethernet 0/1
Switch(config-if)# switchport mode trunk
Switch(config-if)#
%LINEPROTO-5-UPDOWN: Line protocol on Interface GigabitEthernet0/1, changed state to down
%LINEPROTO-5-UPDOWN: Line protocol on Interface GigabitEthernet0/1, changed state to up
Switch(config-if)# end
%SYS-5-CONFIG_I: Configured from console by console
Switch# wr
Building configuration...
[OK]
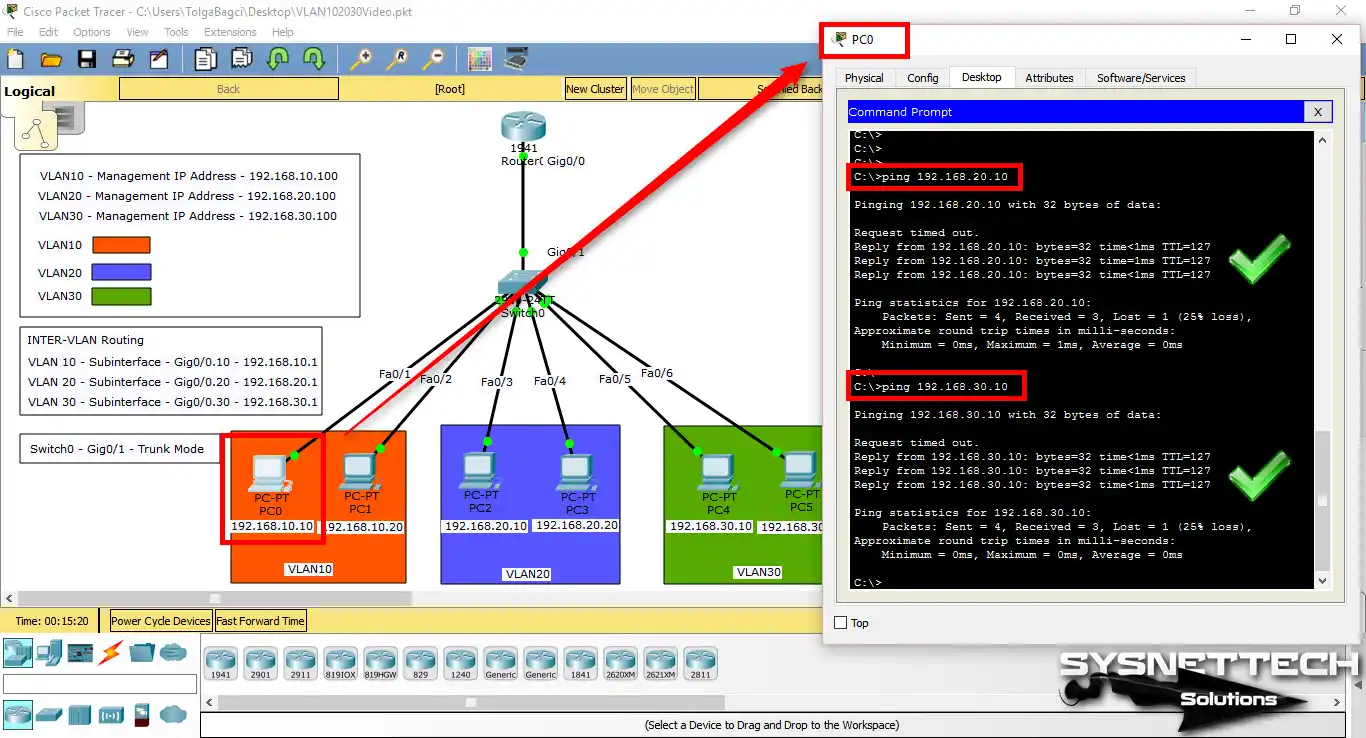
Step 6
Once you have completed the Inter-VLAN routing steps, you can see that the operation was successful when you ping PCs that are members of other VLANs via PC0.
Show Commands for Inter-VLAN Routing
- Router – IP Interface Brief
- Switch – Trunk Port Info
- Router – Running Config
- Switch – Running Config
Router# show ip int br
Interface IP-Address OK? Method Status Protocol
GigabitEthernet0/0 unassigned YES unset up up
GigabitEthernet0/0.10 192.168.10.1 YES manual up up
GigabitEthernet0/0.20 192.168.20.1 YES manual up up
GigabitEthernet0/0.30 192.168.30.1 YES manual up up
GigabitEthernet0/1 unassigned YES unset administratively down down
Vlan1 unassigned YES unset administratively down downSwitch# show interfaces gigabitEthernet 0/1 switchport
Name: Gig0/1
Switchport: Enabled
Administrative Mode: trunk
Operational Mode: trunk
Administrative Trunking Encapsulation: dot1q
Operational Trunking Encapsulation: dot1q
Negotiation of Trunking: On
Access Mode VLAN: 1 (default)
Trunking Native Mode VLAN: 1 (default)
Voice VLAN: none
Administrative private-vlan host-association: none
Administrative private-vlan mapping: none
Administrative private-vlan trunk native VLAN: none
Administrative private-vlan trunk encapsulation: dot1q
Administrative private-vlan trunk normal VLANs: none
Administrative private-vlan trunk private VLANs: none
Operational private-vlan: none
Trunking VLANs Enabled: ALL
Pruning VLANs Enabled: 2-1001
Capture Mode Disabled
Capture VLANs Allowed: ALL
Protected: false
Appliance trust: none
Switch#Router# show running-config
Building configuration...
Current configuration : 891 bytes
!
version 15.1
no service timestamps log datetime msec
no service timestamps debug datetime msec
no service password-encryption
!
hostname Router
!
no ip cef
no ipv6 cef
!
license udi pid CISCO1941/K9 sn FTX15243C2U
!
spanning-tree mode pvst
!
interface GigabitEthernet0/0
no ip address
duplex auto
speed auto
!
interface GigabitEthernet0/0.10
encapsulation dot1Q 10
ip address 192.168.10.1 255.255.255.0
!
interface GigabitEthernet0/0.20
encapsulation dot1Q 20
ip address 192.168.20.1 255.255.255.0
!
interface GigabitEthernet0/0.30
encapsulation dot1Q 30
ip address 192.168.30.1 255.255.255.0
!
interface GigabitEthernet0/1
no ip address
duplex auto
speed auto
shutdown
!
interface Vlan1
no ip address
shutdown
!
ip classless
ip flow-export version 9
!
line con 0
line aux 0
line vty 0 4
login
!
endSwitch# show running-config
Building configuration...
Current configuration : 1638 bytes
!
version 12.2
no service timestamps log datetime msec
no service timestamps debug datetime msec
no service password-encryption
!
hostname Switch
!
spanning-tree mode pvst
!
interface FastEthernet0/1
switchport access vlan 10
switchport mode access
!
interface FastEthernet0/2
switchport access vlan 10
switchport mode access
!
interface FastEthernet0/3
switchport access vlan 20
switchport mode access
!
interface FastEthernet0/4
switchport access vlan 20
switchport mode access
!
interface FastEthernet0/5
switchport access vlan 30
switchport mode access
!
interface FastEthernet0/6
switchport access vlan 30
switchport mode access
!
interface GigabitEthernet0/1
switchport mode trunk
!
interface Vlan1
no ip address
shutdown
!
interface Vlan10
mac-address 0002.4ad8.4b01
ip address 192.168.10.100 255.255.255.0
!
interface Vlan20
mac-address 0002.4ad8.4b02
ip address 192.168.20.100 255.255.255.0
!
interface Vlan30
mac-address 0002.4ad8.4b03
ip address 192.168.30.100 255.255.255.0
!
line con 0
line vty 0 4
login
line vty 5 15
login
!
end
Switch#Video
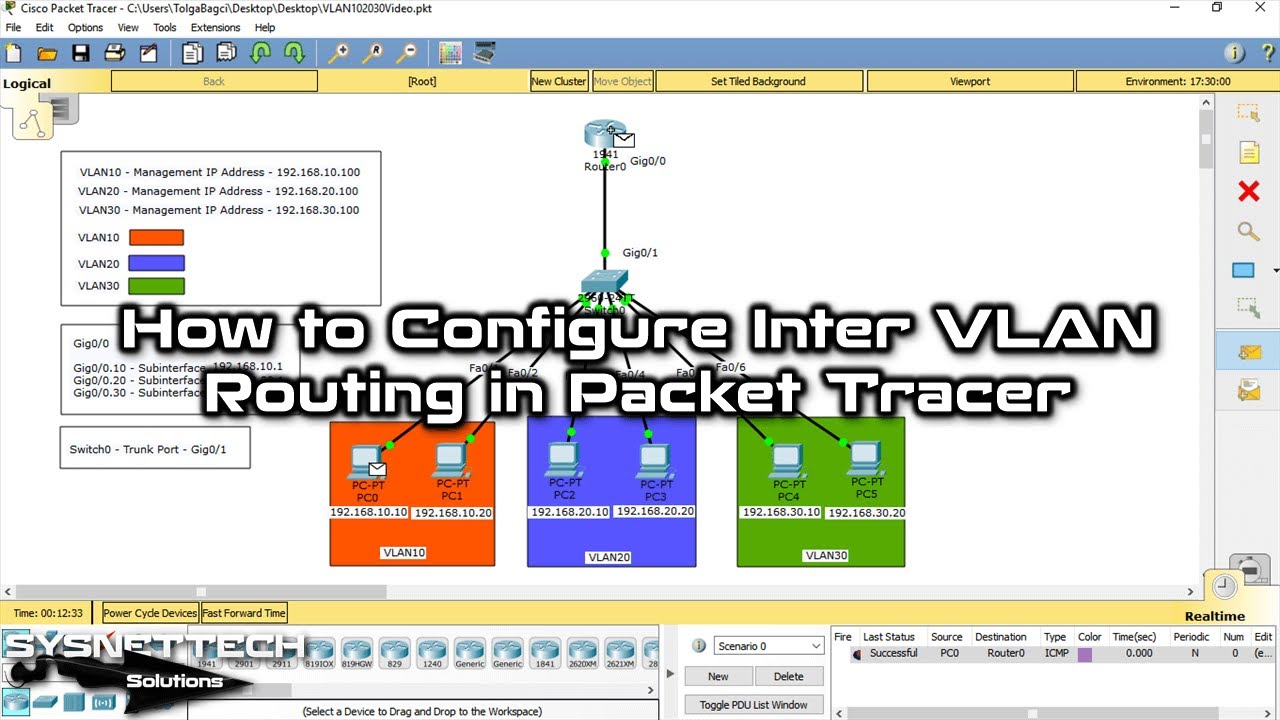
You can watch the video below for Inter-VLAN settings on the Switch and Router, and also subscribe to our YouTube channel to support us!
Conclusion
In this article, we have examined step by step how to make Inter-VLAN routing on a Switch with the Packet Tracer simulator. Thanks for following us!

1 Reader Comment
Hello. These series of articles have enlightened me on how to configure cisco devices for VLANs and make better use of a 1941 router for VLAN support. Thanks.