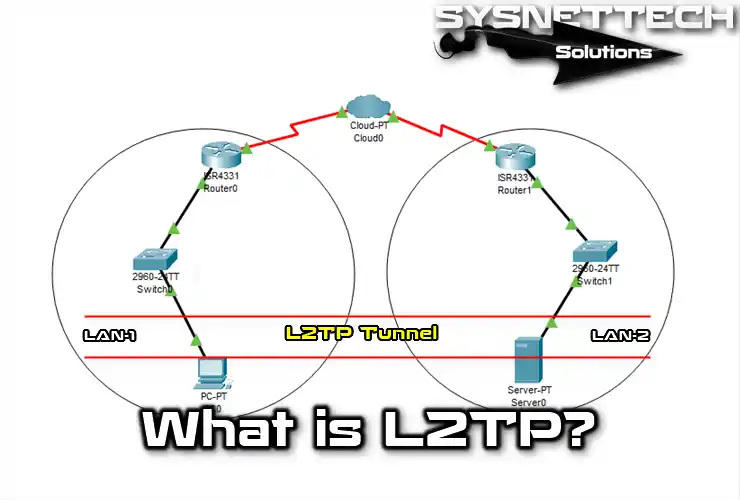
L2TP (Layer 2 Tunneling Protocol) is a safe way to make a VPN tunnel. This way mixes parts of PPTP and L2F. Because of this, it makes a safer way to connect. It also gives a strong base for sending data.
L2TP is a standard made by the IETF group. Its rules are written down in a paper called RFC 2661. This method wraps data in a safe tunnel. So, this makes starting a VPN much simpler.
This way lets people join faraway networks like a local one. It also adds another level of safety for all sent data.
L2TP gives users strong data privacy and keeps it correct. This is because it often teams up with something like IPsec. Because of this, private details are safe from being listened to and changed.
Also, L2TP allows safe talking between faraway places. So, it has a massive job in today’s network systems.
What is the L2TP Protocol for Secure VPN Connection?
Microsoft and Cisco’s network engineers worked together to develop L2TP in 1999. This protocol uses UDP port 1701. It also tunnels network traffic over inactive PPP connections. Also, it supports remote dial-up connections like POTS and ISDN.
The L2TP protocol is vital in VPN (Virtual Private Network) tech. Also, ISP companies use it to provide secure connections to their customers.
With this protocol, data transfer works for many packet types, including X.25, Frame Relay, and ATM. It also has authentication methods like PPP, PAP, and CHAP for setting up telephone connections. Also, it supports the use of control systems like RADIUS.
L2TP History
If we look at the history of L2TP, we see that it laid the foundation for today’s VPN connections. Its development dates back to the emergence of the Internet. So, they developed this protocol because there was a need for secure communication in PC networks.
As we mentioned before, L2TP (Layer 2 Tunneling Protocol) has evolved with the pros of these two protocols:
- PPTP (Point-to-Point Tunneling Protocol)
- L2F (Layer 2 Forwarding Protocol)
The previous version of L2TP is L2F. However, thanks to the new updates, it has become more efficient.
After the IETF (Internet Engineering Task Force) standardized L2TP in 1999, its use increased to ensure security in data flow. It worked by integrating many network devices and software at that time.
Later on, Microsoft included this protocol in its developed operating systems. That’s why it became much easier for users to set up an L2TP-based VPN connection.
With its increasing use, L2TP started to cause some security problems. So, they started using it with IPsec to protect data health further.
IPSec and L2TP
Users who want to connect to corporate networks can use L2TP. However, since this connection traffic is not encrypted, you must use IPSec to ensure network security.
We usually refer to it as L2TP over IPSec because it secures data with IPSec.
IPSec (Internet Protocol Security) verifies IP traffic in a communication session. Also, it encrypts data in the network flow and provides safety.
IPSec is a system that uses special codes for sessions in a network. This helps ensure that local and remote destinations can check each other’s identities for every session.
PPTP is a more straightforward way to wrap up data. That’s why it uses a cheap encryption method called RC4, which is affordable and doesn’t strain the processor.
L2TP typically uses security methods called 3DES and AES through IPSec. This gives it a much more complex way of wrapping data, going up to six layers.
Using hardware-based 3DES encryption in a system provides more security and efficiency. Thus, using this encryption process with an app strains the running system and reduces its performance.
Features of the L2TP Protocol
The L2TP/IPSec protocol, a standard method for PPTP and L2F, basically uses a double-wrapping technique. So, its use alongside IPSec is standardized by RFC 3193.
The first wrapping sets up the PPP connection, and the second creates the IPSec encryption. This method first processes the traffic through the L2TP protocol. Then, it adds an extra layer of security to this form. As a result, it’s safer than PPTP but works more slowly.
You create extreme data traffic using the L2TP protocol with the AES encryption algorithm. One important thing to know is that this protocol doesn’t provide encryption security.
A packet frame and UDP wrapping make up a layer two tunnel. An IP packet encloses the source and destination addresses, identifying both ends of the tunnel.
In addition, the Layer 2 Tunneling Protocol is compatible and works seamlessly with NAT. This way, it provides a professional solution for many homes or business networks.
How Does the L2TP Protocol Work?
The process of creating a VPN connection with this protocol includes the following steps:
- IKE (Internet Key Exchange) typically forms IPsec SAs (Security Associations). First, it initiates a connection over UDP port 500. It then uses a shared password, public keys, or X.509 certificates on both devices.
- It performs ESP (Encapsulating Security Payload) encapsulation in transport mode. The IP protocol number for the ESP is 50.
- It creates a secure channel until this step, but the tunnel has yet to be made.
- Establishing a layer two tunnel between SA endpoints begins.
- It does IPsec encryption through the SA’s secure channel. Then, it starts wrapping the packets between the endpoints.
- In this case, an IPsec packet hides the data traffic. This means it encrypts the source and destination IP addresses in the package.
- It creates a secure channel to carry PPP packets using the IP protocol. This ensures and maintains the privacy of all data within this channel.
- As a result, IPsec provides security, while the L2TP protocol makes a tunnel. It keeps things secure for you.
L2TP Advantages and Disadvantages
Now, let’s explore the good and not-so-good parts of Layer 2 Tunneling Protocol:
Pros of This Protocol
- Security
It keeps your data safe and travels to its destination. This means it protects your essential info. When teamed up with IPsec, it becomes even more secure.
- Multi-Protocol Support
Many network devices and operating systems support the L2TP protocol. This is because it offers multi-protocol help. Thus, users can create secure access even between different platforms.
- Ease of Configuration
Since it integrates with Windows systems, setting up and configuring it is pretty straightforward. That’s why users can quickly and easily establish a VPN connection.
- Flexibility
Due to its support for multiple protocols, it operates flexibly in various ways.
- Communication Channels
It securely delivers info thanks to its contact channel routing feature. That’s why it works well when handling network traffic.
Cons
- Connection Speed
Sadly, this protocol can be slow, especially for high-bandwidth tasks.
- Resource Consumption
It consumes quite a lot of resources compared to other VPN methods. So, this can be a problem for devices with lower hardware capabilities.
- Other VPN Protocols Comparison
It has disadvantages in terms of security and speed compared to others. For instance, it lags in terms of pace compared to PPTP.
- Updates and Security
Because of security weaknesses, users had to use this protocol with IPsec.
Protocol Packet Structure
The packet structure of the L2TP protocol, which plays an active role in VPN connections, is as follows:
- Header
The first part of the packet structure contains the header. In this case, other devices notice it. So, it is 8 bytes long:
- Version Number: This part shows the protocol version used. It’s like a unique code.
- Length: It tells how big the header and data are together.
- Tunnel ID: It points to a particular ID inside the L2TP tunnel.
- Session ID: This special ID shows which session has the data. Think of it as a session label.
- PPP Protocol: It describes the types of data PPP sends. Think of them as data groups.
- Data Field
Here, data waits to move between devices. So, it keeps PPP packets safe while traveling.
- Extension Header
It’s like an extra part. Users rely on it for security or more routing information.
- Encapsulation
During PPP use, it wraps user data. The device receives it unpacked.
How to Install L2TP VPN on Windows Systems
Step 1: Get VPN Server Information: First, get data from your VPN provider. Start with the VPN server PC info. Then, remember your username and password to log in.
Step 2: Enter Network and Internet Settings: Start by visiting your PC’s Control Panel tool on Windows 10 & 11. Then, you must choose the Network and Sharing Center option. After that, find and click on “Change Adapter Settings.” Now, open either Ethernet or Wi-Fi settings.
Step 3: Add New VPN Connection: Inside the connection window, you must choose “Add New Connection.” Then, pick “Set Connection” in the open window and click Next.
Step 4: Type VPN Server Information: To enter VPN server information, do the following:
- Connection Name: Write down the place for connecting to work or a particular spot.
- Server Name or IP Address: Enter the address of the VPN server you obtained.
- VPN Type: Select L2TP/IPsec as the type.
- Security Type: Select EAP-MSCHAP v2 as the better security type.
- Username and Password: Type the credentials for the connection.
Step 5: Save Connection and Connect: Finally, click Manage Connections from the Network and Sharing Center location. Next, select the VPN connection you just added, right-click, and click Connect. Thus, you can set up your L2TP VPN connection from your Windows computer.
Comparing L2TP with Other Protocols
Here is a summary table for you to better understand the Layer 2 tunneling protocol by comparing the old and new ones:
| Features | L2TP | PPTP | OpenVPN | IPsec |
|---|---|---|---|---|
| Security | Moderate | Low | High | High |
| Speed | Moderate | High | Moderate | High |
| Ease of Use | Easy | Very Easy | Moderate | Moderate |
| Cross-Platform Support | Yes | Yes | Yes | Yes |
| Encryption | Yes (with IPsec) | Yes | Yes (with SSL/TLS) | Yes |
| Open Source | No | No | Yes | Yes |
| Connection Stability | Good | Good | Good | Good |
| Application Support | Wide | Limited | Wide | Wide |
| NAT Compatibility | Yes | Yes | Yes | Yes |
| Update Status | Current | Outdated | Current | Current |
| Mobile Support | Yes | Yes | Yes | Yes |
Frequently Asked Questions (FAQ)
- What is L2TP used for?
- Is L2TP a good VPN?
- What is the difference between L2TP and PPTP?
- What is the difference between L2TP and IPSec?
Conclusion
As a result, Layer 2 Tunneling Protocol has an essential place in secure VPN technologies. It also successfully combines the strengths of its predecessors, PPTP and L2F.
It also works well with IPSec, making data transfer safer. At the same time, it keeps network sessions correct and secure. Because it is strong, it works well in different networks.
In addition, it also facilitates safe communication between businesses and people. More people need secure remote access. So, it provides both safety and speed in the digital world. So, in short, this makes it a trusted and valuable choice.

Be the first to share your comment