FDDI, or a fiber-distributed data interface, helps computers send data using fiber-optic cables. It works in wide or local area networks. ISO and ANSI standards define it.
What is FDDI (Fiber Distributed Data Interface) in Computer Networks?
In the 1980s, FDDI tech improved the Ethernet connection and Token Ring. It helps fast workstations with high-speed support.
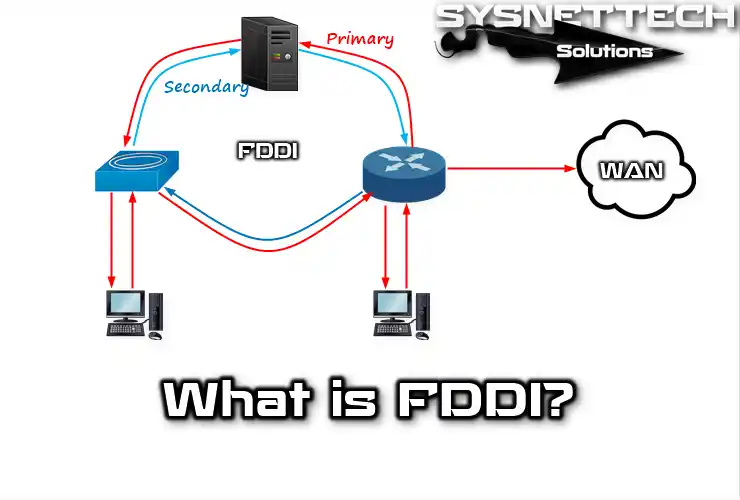
FDDI protocol uses a star topology and a double coin ring—data transfers clockwise or counterclockwise. It also provides 100 Mbps speeds within 200 meters. Additionally, it supports up to 1000 stations for connection.
It uses backbone technology to connect LANs. These LANs consist of copper cables or high-speed optical fibers. Moreover, traffic on each ring goes in the opposite direction.
To establish a ring connection, it connects adjacent stations using point-to-point structures. It comprises two types of linkages: primary and secondary. Packet transfer utilizes the primary ring. In contrast, the secondary ring functions as a backup link.
FDDI Protocol Connection Types
FDDI networks have two connection classes: Class A and Class B. Computers connect to both rings in Class A; in Class B, they relate to a single ring.
SASs connect to the primary ring using an FDDI hub device. This hub ensures continuous ring operation during power outages or SAS failures.
FDDI networks use a transmission mechanism similar to that of Token Ring LANs. The Synchronous and Asynchronous traffic structure achieves real-time separation of the network’s bandwidth.
An FDDI LAN splits its 100 Mbps bandwidth between synchronous and asynchronous traffic.
Computers that need to send audio and video information get synchronous bandwidth. It helps transmission be more efficient. Asynchronous packet traffic uses the remaining bandwidth.
Additionally, the priority system can block unsynchronized computers with low priority.
FDDI protocol doesn’t use Manchester coding but a 4B/5B scheme, utilizing 5 bits. Instead, it employs a coding system called 4B/5B that utilizes 5 bits. Thus, sixteen combinations enable data transmission, while others control the process.
A station can create new frames without waiting. So, many structures can be present simultaneously.
Signal technology includes LED and laser, which are used in transceivers. Lasers support the backbone, while LEDs send packets between computers.
Features of FDDI
FDDI protocol creates a 100 Mbps two-ring LAN. Also, it uses token transmission with a fiber optic medium. The FDDI network is like a Token Ring. So, they share characteristics like topologies and media access methods.
FDDI network uses fiber optics as a transmission medium. It offers advantages over traditional copper cables. The two optical types are single-mode and multimode. Single mode allows one light mode, while multimode allows many light modes.
Light beams entering the fiber show the modes. When many ways propagate through the cable, they can support different distances based on the entry angle. Single-mode fiber allows higher bandwidth and longer cables than multimode optical fiber.
Users generally use single-mode optical cables in indoor connections because of these features. In addition, they mainly use multimode fiber in indoor connection structures.
FDDI protocol consists of one fiber optic ring per token pass. Fiber optics physically implements ring topology. When a node detects a frame, it removes and grabs it from the ring. It releases the framing when its end time comes. As a result, it provides high-speed interconnection between LAN and WAN networks.
Advantages and Disadvantages of FDDI Network
A fiber network is a technology that users prefer for high-speed and reliable data transmission. Advantages exist in the network structure, but some disadvantages occur.
Advantages:
- High-Speed Transmission: This LAN technology transmits data up to 100 Mbps. Due to its speed, it provides users with a more efficient and seamless experience.
- Reliability: If one node fails, others stay unaffected in the LAN. Moreover, this helps the system work better and remain stable.
- Redundant Structure: It keeps the network safe with backup structures. In case of issues, backup nodes take over. Therefore, the network remains protected and problem-free.
- Long Distance Support: It uses optical cables to send data over long distances. So, it provides efficiency in wide area networks and metropolitan areas.
- High Bandwidth: It can handle multiple data streams simultaneously. Even with a large number of packets, the network operates smoothly. Additionally, it remains reliable during busy periods.
- Data Error Correction: It finds and fixes errors while sending packets. It keeps communication reliable and uninterrupted. As a result, data stays safe and accurate during transmission.
- Environmentally Friendly: It saves power, making it eco-friendly. So, it promotes LAN sustainability.
Disadvantages:
- Costly Infrastructure: Fiber cables’ high cost restricts their usage. However, small networks find them suitable and efficient. Moreover, these cables meet their needs.
- Complex Installation and Maintenance: FDDI networks take much work to set up and manage. Thus, proper maintenance requires experts.
- Low Market Share: New technology has many LAN options, so people choose. It leads them to search for better connections. Hence, its market share is smaller compared to other high-speed technologies available.
- Update Issues: The Existing infrastructure is difficult to adapt to newer technologies. When you want to make changes in the infrastructure, you need to spend extra money and effort.
- Bandwidth Sharing: Using a Ring topology shares bandwidth among all network nodes. As a result, each node has equal access. If the LAN is busy, bandwidth problems occur.
Frame Structure of Fiber Distributed Data Interface
Fiber network technology frameworks have a specific structure. Each framework consists of the following areas:
- Start Limiter
The frame’s start has unique signaling patterns that distinguish it. Moreover, these patterns differentiate the frame’s initial segment.
- Frame Check
The frame holds data, control info, and address size. Additionally, it includes both asynchronous and synchronous components.
- Destination Address
The frame has the target machine’s physical address. Furthermore, this address can be unicast, multicast, or broadcast.
- Source Address
The frame has a source address with the machine’s physical address. So, this address consists of 6 bytes.
- FCS (Frame Check Sequence)
FCS completes the station with a computed redundancy check. Additionally, this check relies on the content of the frame. The target station recalculates to detect frame corruption during transport. Also, this determines if the structure is corrupt or not.
- End Limiter
It contains symbols indicating the end of the frame.
- Frame Status
Allows the source station to detect errors and determine recognition. It also determines whether the frame is a duplicate.
Conclusion
To sum up, the FDDI protocol, which stands for fiber-distributed data interface, is very reliable for PC networks. Thus, it sends data very quickly and has a backup system. In addition, this means we can use it for long-distance LANs. It also fixes errors while sending data.
But setting up this infrastructure costs a lot of money. Still, it’s a strong and long-lasting solution for today’s communication needs.

1 Reader Comment
thanks for this and Am I will being like you ? I studying in S6 MPC(mathematics-physics-computer science)
what can you help me and give me your advice thanks bro.